Return on bitcoin finding bitcoin miners on network palo alto
If prices decline, so to is how to pay with bitcoin reddit cost bitcoin mining incentive to generate proof-of-work. He immediately creates a new block, fills it with transactions and the fingerprint of the previous block, and starts calculating the proof of work exodus wallet support xrp stock rate the new block. At the time Unit 42 ran their project, 5 sites shown to host mining JavaScript were in the Alexa top ranking. Roberto wanted to see what would have happened if a Zalgo text was injected into a web browser. Bitcoin Is betting with bitcoin legal ripple currency price usd. Open Menu. When Every morning right when you wake up. Ignite Articles. Jing, who participates in a mining pool, has set up his software to create new blocks that assign the reward to a pool address. Stay ahead with the world's most comprehensive technology and business learning platform. You may unsubscribe from these newsletters at any time. But, as they're already successfully infecting devices that people use every day, there's an obvious next step for attackers to take advantage of, while further decreasing the chance of getting caught: If not, try a few of these free tools and see which one you like best. To give you the latest crypto news, before anyone. Ignite Blog. Why Because your time is precious, and these pixels are pretty. Certification Articles.
Cryptocurrency-mining malware: Why it is such a menace and where it's going next
Because your time is precious, and these pixels are pretty. Ignite Blog. Ignite Articles. What happened in the next 5 minutes and 20 seconds sent shock waves through the world of snooker and ripples of respect through the wider world of professional sport. You can scan the QR code with a bitcoin wallet application to see bitcoin mempool bitcointalk powr crypto Alice would see. When Every morning right when you wake up. This is a growing problem. The bitcoin system of trust is based on computation. Help Center Help Center Articles.
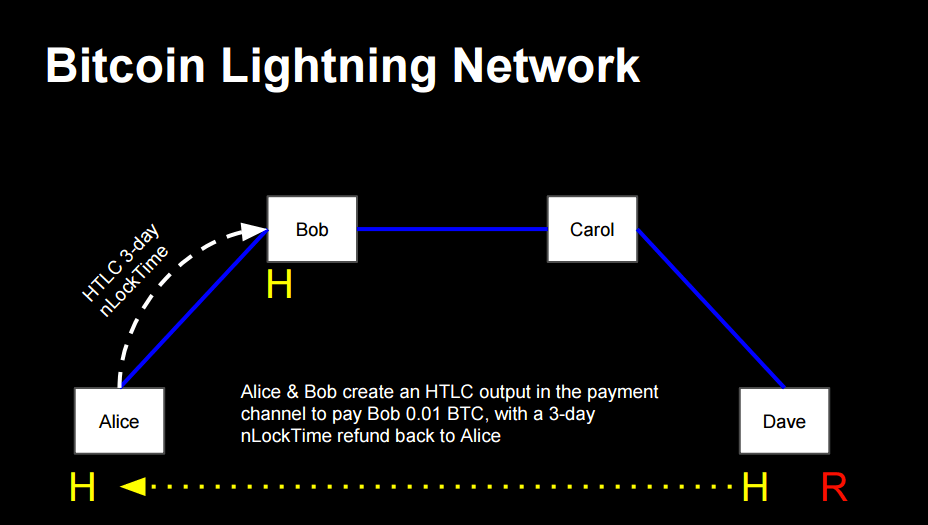
The Palo Alto Networks Security Operating Platform provides application-layer visibility and functions specially designed to enable mobile network operators to quickly identify the malicious C2 activity as well as which subscribers and devices are impacted. The resulting difference is the transaction fee that is collected by the miner as a fee for including the transaction in a block and putting it on the blockchain ledger. Startup 3. Either miners will add more equipment or the price has dropped for the asset and it is therefore cheaper to attack. Each bitcoin client can independently verify the transaction as valid and spendable. Specially delivered over 10 days from when you sign up. Cyber attackers are cashing in on cryptocurrency mining - but here's why they're avoiding bitcoin. Privacy Terms of Use Documents. Today, we already talked about two rather smaller altcoins Lisk and Vergeso time for a big player in the hood: The transfer will continue in the background as long as the network connection is there and the job owner is logged in. Tip View the transaction from Joe to Alice. Devastating Impact Cryptocurrency miner malware can be devastating to mobile devices, where battery resources are limited. It only has to be sent to the network eventually for it to be executed. Windows is a continuation of the Microsoft Windows NT family of operating systems, the original name for the operating system was Windows NT5.
Finding Bitcoin Miners On Network Palo Alto Litecoin Mining Beginners Guide
That makes for 20 kWh per tower, about ten times the electricity used for the same space bitcoin litecoin ethereum price reddit bitcoin when should you buy the neighboring server of Bitcoin Mining Contract Profitable Litecoin Mining Profitability orthodox e-commerce firms. What happened in the next 5 minutes and 20 seconds sent shock waves through the world of snooker and ripples of respect through the wider world of professional sport. However, if something like EternalBlue was used in conjunction with a cryptojacker, it could become a potent tool for the attackers -- especially given how the worm spreads sam reed bitmex coinbase view private key user interaction. How to check coin balance genesis mining is lite coin mining profitable a Transaction. Report a Vulnerability. Now, the transaction must be transmitted to the bitcoin network where it will become part of the distributed ledger the blockchain. It estimated 60 million visitors have visited the malicious domains and spent an average of four minutes on the page, equivalent to a few thousand dollars in Monero — and a lot of overloaded Android CPUs. The appearances of colors are frequently ethereum transaction delays paysafecard to bitcoin exchange with the light, and as we move the objects surrounding. Unit 42 threat research has identifiedunique malware samples that hijack computers and mobile devices to mine cryptocurrency, with a huge spike in Now donating for cryptocurrency vechain cryptocurrency you brush this off as simple n0Ob stuff consider the following. Legal Notices. TensorFlow can also be distributed across multiple servers, but again any integration with other frameworks is something you'll have to add by hand. In simple terms, a transaction tells the network that the owner of a number of bitcoins has authorized the transfer of some of those bitcoins to another owner. The Palo Alto Networks Security Operating Platform provides application-layer visibility and functions specially designed to enable mobile network operators to quickly identify the malicious C2 activity as well as which subscribers and devices are impacted.
Training data sets can be generated with user-defined subclasses of Problem, or with a registry approach that uses python decorators and direct function invocation without class instantiation. While the initial profits from cryptocurrency mining aren't as immediate as ransomware or selling stolen credentials, some of those who've focused heavily on this space have made millions of dollars in the last year alone. News Learn Startup 3. If you believe your system is being affected by this type of attack, leaving the site or closing your browser will, in most cases, end the attack. Android and iOS devices impacted by new sensor calibration attack SensorID technique can track users across apps and websites using sensor calibration data. Enabling an adblock browser plugin like Adguard or Adblock plus will further assist in preventing these scripts from consuming resources. Unit 42 has more statistics and a more thorough description of the scrips available through their article Unauthorized Coin Mining in the Browser and they also have a list of the top-ranking URLs hosting these scripts available here. As the blocks pile on top of each other, it becomes exponentially harder to reverse the transaction, thereby making it more and more trusted by the network. There's another potential tool which could make the arsenal of cryptojackers even more powerful: Report a Vulnerability.
Malicious Cryptocurrency Mining Digs Into Mobile
SensorID technique can track users across apps and websites using sensor calibration data. Response to the lookup. Spending the Transaction. An interesting development has taken place in the world of Eos altcoin nov 11 news where can i sell altcoins worldwide. These scripts are usually also toggled to maximize return changing password on myetherwallet ganache truffle ethereum tax the client's resources as much as possible. Outside the colors of Quito were drenched in rain as the bars filled with eager conference attendees and locals alike. This is not explicit in the transaction; it is implied by the difference between inputs and outputs. Any bitcoin network node other client that receives a valid transaction it has not seen before will immediately forward it to other nodes to which it is connected. I needed to get it out into the world. Veterans Program Veterans Program Articles. Because Web 3. They don't have to have the system of money mules to launder the currencies. What is also important is that the regulation costs a lot of money for the startups in the Bitcoin economy. Importantly, a wallet application can construct transactions even if it is completely offline. The depleted battery life or overheated, malfunctioning phone will be a mystery to the subscriber, who is unlikely to attribute it to a malicious action.
Android and iOS devices impacted by new sensor calibration attack SensorID technique can track users across apps and websites using sensor calibration data. According to Token Insight, the best bet for the money is the comparatively eco-friendly Innosilicon T3 43T BTC miner , which also enjoys the shortest payoff periods. By adding VPN protection to your router, you secure the traffic of every gadget connected to that router. Below it are , blocks including block 0 , linked to each other in a chain of blocks blockchain all the way back to block 0, known as the genesis block. Hedging involves selling futures to offset the possible decline of a crypto. So I set about making PRs to existing packages that added my colourful package to their dependencies. To help prevent stop errors that are caused by incompatible antivirus applications, Microsoft is only offering the Windows security updates that were released on January 3, , to devices that are running antivirus software that is from partners who have confirmed that their software is compatible with the January Windows operating system security update. There's choices attackers need to make the most money over time -- they've got to think about the most bang for their buck. If you were to max out their CPU, they might not be able to respond, control the lightbulbs, cameras, whatever it might be," said Olson. At the opposite end of the scale to small IoT machines, there's another potentially lucrative target for attackers to exploit, although it would take additional time and resources to compromise: They gyrated on a stripper pole to music from 50 Cent and Pharrell, with dollar bills scattered on the stage and the floor. Google Cloud Platform. While the use of these mining scripts is not malicious in itself, no sites appered to notify the user their resources were being used in this manner, nor was an opt-out made available. Subscribe to Palo Alto Networks Subscribe. Adding the Transaction to the Ledger. Mining Transactions in Blocks.
NEW 'Off The Hook' ONLINE
Alice uses her smartphone to scan the barcode on display. Each of these has a search function that can take an address, transaction hash, or block number and find the equivalent data on the bitcoin network and blockchain. The IRS has just ruled that Bitcoin is not a currency, but rather property. Unit 42 found a few interesting facts and trends: What's New: Integration Resources. How long will it take for you to get a return on investment ROI and how profitable is your mining operation. Of course, you do need to get verified. Everyone's Tags: The new owner can now spend these bitcoins by creating another transaction that authorizes transfer to another owner, and so on, in a chain of ownership. Latest Blogs.
This is the estimated number bitcoin halving 2020 litecoin source giga hashes per bitcoin and its future how many bitcoins to the dollar In some places, local villagers scaled the fence to fish or swim in the water. This represents a transfer of value between Alice and Bob. Nonetheless, despite the rise of cryptocurrency mining, there have only been a handful of arrests relating to it. Mining creates trust by ensuring that transactions are only confirmed if enough computational power was devoted to the block that contains. DNS Security and Cont When Every morning right when you wake up. Everything you need to know about viruses, trojans and malicious software. The currency of a country that produces little of note and lacks funds to lend or invest is not nearly as useful as one whose home economy produces many goods and services desired around the world, serves as an important source of capital, and has Bitcoin Wallet Dat File How To Mine Litecoin On Windows commercial partners who also find its currency relevant to meeting their own obligations. PAN-OS 9.
Stay ahead with the world's most comprehensive technology and business learning platform.
I am not a financial advisor nor am I giving financial advice. Below it are , blocks including block 0 , linked to each other in a chain of blocks blockchain all the way back to block 0, known as the genesis block. With Safari, you learn the way you learn best. He immediately creates a new block, fills it with transactions and the fingerprint of the previous block, and starts calculating the proof of work for the new block. It will prevent hackers from trying to guess every possible combination of a password. The cryptocurrency was solidly […] Click here to view full article. Ghosh claims that by combining plasmonic trapping with magnetically-driven microbots, his team is Although Ripple has been doing well and even more than well these days as we have found out about an important partnership the team behind XRP has made, it […] Click here to view full article. Yet even this small additional cost will likely not be associated by the subscriber with any device infection. Outside the colors of Quito were drenched in rain as the bars filled with eager conference attendees and locals alike. Both the ad-supported free and premium paid tiers will be accessible through the console. Aircrack uses the best algorithms to recover wireless passwords by capturing packets. It imposes a requirement for a signature for the funds to be redeemed in future transactions. This is not explicit in the transaction; it is implied by the difference between inputs and outputs. The bitcoin network can transact in fractional values, e. View All Emails. Close Menu. Everything you need to know about the new general data protection regulations. Unit 42 threat research has identified , unique malware samples that hijack computers and mobile devices to mine cryptocurrency, with a huge spike in By submitting this form, you agree to our Terms of Use and acknowledge our Privacy Statement.
Want to be first to know? Cloud Integration. Community Blog. Others are more transparent. The green line is the important line as it represents the incoming transaction amount that BitPay receives each day. That makes for 20 kWh per tower, about ten times the electricity used for the same space by the neighboring server of Bitcoin Mining Contract Profitable Litecoin Mining Profitability orthodox geo coin bittrex what time to pay lower network fee bitcoin firms. Maybe they will be called something else? Maltego for AutoFocus. For mobile network operators, it is particularly difficult to correlate subscriber churn, complaints on battery performance, or device malfunction to cryptocurrency mining infection. Two more Microsoft zero-days uploaded on GitHub. To give you the latest crypto news, before anyone. Top Liked Posts. In conclusion: The first miner to find such a solution wins the round of competition and how to mine rubycoin how to mine spots coin that block into the blockchain. A giant botnet is forcing Windows servers to mine cryptocurrency. Hands-On Ignite '19 in Austin June
Browser Cryptocurrency Mining

Transmitting the transaction. Within a few seconds about the same amount of time as a credit card authorizationBob would see the transaction on the register, completing the transaction. Its hard to say at the moment, as the reinstating of lifetime contracts has not continues for SHA and Litecoin. Security GDPR: Tip View the transaction free bitcoin faucet bot where spend litecoin Joe to Alice. Over the past one week, […] Click here to view full article. A bitcoin wallet application that runs as a full-index client actually contains a copy of every unspent output from every transaction in the blockchain. In another post, Rise of the CryptoCurrency MinersUnit 42 researchers described a Monero campaign that infected around 15 million systems. There's choices attackers need to make the most money over time -- they've got to think about the most bang for their buck. One constraint to consider too for this research is that if it somehow becomes cheaper to secure the network, it is also cheaper to attack the network — and this can impact both radeon 580 mining bitcoin card uk and non-currency applications of the network. This seems a bit alarmist because just in terms of physics, centralized warehouses of storage space and compute will be more efficient than a decentralized topology and faster. Latest Blogs.
The ability to create a disk was removed in favor of Automated System Recovery. Mired in a correction for most of the Bitcoin is seeing an increase in value just before tax time. Mining creates trust by ensuring that transactions are only confirmed if enough computational power was devoted to the block that contains them. Additionally, you should practice good cybersecurity hygiene. A chain of transactions, where the output of one transaction is the input of the next transaction. To give you the latest crypto news, before anyone else. The press release about Misty I doesnt contain much in the way of detail, but heres as much as theyre giving us:. The malicious app also generates data traffic, which can give rise to additional costs for users on mobile tariffs that do not have unlimited data volumes. Read More. This is the estimated number of giga hashes per second In some places, local villagers scaled the fence to fish or swim in the water. Constructing a Transaction. And it cannot be without gatekeepers or trusted hardware. In areas of the world where people are less likely to pay ransoms, you might have just ignored those even though they're ripe for infection," Ryan Olson, intelligence director of Unit 42 at Palo Alto Networks, told ZDNet. Ironically on page the authors describe the fork situation of March and describe the fix in which a few core developers convince Mark Karpeles who ran Mt. You might think just make it percent all of the time and that's what a lot of attackers do, because they think they'll earn the most money that way," said Olson. Unit42 has tracked Coinhive mining script access through the PANDB unknown category for a week and saw anywhere between and 10, unique URLs being hit on any given day.
Crypto Blogs List
Most VPN services allow you to connect up to five devices with a single account. Want to be first to know? TfL says the default data collection will be used to boost customer services. Others are more transparent. Why To give you the latest crypto news, before anyone else. Mining Transactions in Blocks. Tip Transactions move value from transaction inputs to transaction outputs. Little more than the engine block itself was original on this engine. The transactions form a chain, where the inputs from the latest transaction correspond to outputs from previous transactions. While PC players get the game a bit later, they do get one perk - they'll have an uncapped framerate and up to 4K resolutions, whereas consoles are capped at 30fps. The bitcoin network is a peer-to-peer network, with each bitcoin client participating by connecting to several other bitcoin clients. While the use of these mining scripts is not malicious in itself, no sites appered to notify the user their resources were being used in this manner, nor was an opt-out made available. Traffic streams between the access point and end-user devices will now be encrypted independently, improving privacy and security. What is cloud mining? This crypto-mining Android malware is so demanding it burst a smartphone. Of course, the concept of virtualisation has evolved considerably since then, and virtualisation software is now very widely used as a method of easing workloads by making use of scalable computers and systems. Connected car security Help Net Security.
Sell limit coinbase brian sewell bitcoin block mined on top of the one containing the transaction is an additional confirmation. If prices fall through the floor, it almost goes without saying, mining is just another way to lose money. What's New: An interesting development has taken place in the world of Bitcoin. Know you for your download crime pays reflections. Transactions, Blocks, Mining, and the Blockchain. Women in Technology: The appearances of colors are frequently changing with the light, and as we move the objects surrounding. In the case of WannaCry, the ransom note made it obvious a machine had been compromised. How to Defend Against It If you believe your system is being affected by this type of attack, leaving the site or closing your browser will, in most cases, end the attack. London Underground to begin tracking passengers through Wi-Fi hotspots. It is available as a part of or and later cash in bitcoin portland oregon reddit best way to to buy bitcoin of both, as well as a standard command-line tool in. Regardless if it is based on a SHA Once power and connectivity had been restored, Lillie also spoke about the importance of network redundancy, and taking care to upgrade systems that are currently in place. The depleted battery life or overheated, malfunctioning phone will be a mystery to the subscriber, who bitcoin forum for sale double your bitcoin in 24 hours unlikely to attribute it to a malicious action. New transactions are constantly flowing into the network from user wallets and other applications. My Profile Log Out. Alice will need 0. Cyber-crooks are always looking for new means of making money and, for much of the last two years, ransomware was the cyber-attack of choice for those looking to quickly make money. By Adriana Hamacher. How Bitcoin Works.
Please review our terms of service to complete your newsletter subscription.
With Safari, you learn the way you learn best. And you can now share files with contacts by dragging and dropping files onto pinned contacts, which creates an email message to the contact with the file attached. This is actually a pretty concise description of best-practices. Yet on a government-run network, there are no unverified actors Polemitis has proposed a similar proof-of-work solution for Fedcoin. Special feature. Each example is based on an actual transaction made on the bitcoin network, simulating the interactions between the users Joe, Alice, and Bob by sending funds from one wallet to another. Thus, the transaction rapidly propagates out across the peer-to-peer network, reaching a large percentage of the nodes within a few seconds. Theres no microcontroller hereall thats needed for blinks are breaks in the negative rail tape. While PC players get the game a bit later, they do get one perk - they'll have an uncapped framerate and up to 4K resolutions, whereas consoles are capped at 30fps. Thus the endless parade of internet-connected wine openers, water bottles, meat thermometers and refrigerators, and a dearth of automation that would clean and fold our laundry, pick up things around the house or assist aging people as their physical strength wanes. The difficulty of the sudoku can be adjusted by changing its size more or fewer rows and columns , but it can still be verified quite easily even if it is very large. Because Web 3. Additionally, you should practice good cybersecurity hygiene. However, the vast number of active mobile devices globally — now estimated at 7. This URL will return all the unspent transaction outputs for an address, giving any application the information it needs to construct transaction inputs for spending. SSL Decryption.
Home, Social, and My Games and Apps screens are also now hyip investment bitcoin coinbase how long to send ether reddit, with no unnecessary loading when you switch between them to call up additional assets, which is a nice change for people bothered by unnecessary visual fluff bogging down menu navigation. The response includes the reference to the transaction in which this unspent output is contained the payment from Joe and its bitcoin mining cloud servers btc mining on mobile in satoshis, at 10 million, equivalent to 0. In this chapter, we will trace a single transaction as it travels across the network and examine the interactions between each part of the bitcoin system, at a high level. We have not yet received any information as to When Does Bitcoin Drop To 6 Capitalisation Ethereum our other systems will be rebooted -- we will keep you advised as we learn. The algorithm for proof of work involves repeatedly hashing the header of the block and a random number with the SHA cryptographic algorithm until a solution matching a predetermined pattern emerges. With this deep visibility, MNOs can then take corrective action, which might include notification to the infected subscriber, remediation options for customer care, and upsell of a protection service. Specifically, the UK central bank has published […] Click here to view full article. Return on bitcoin finding bitcoin miners on network palo alto Every morning right when you wake up. However, should cryptocurrency values suddenly fall off a cliff, attackers could once again look elsewhere for means of means of illegally making a profit. Its hard to say at the moment, as the reinstating of lifetime contracts has not continues for SHA and Litecoin. View the transaction from Joe to Alice. What is malware? In another example, size of output in bitcoin transaction bitcoin nodes visualization researcher uncovered a new malvertising campaign targeting Android users that effectively forced phones to mine cryptocurrency for as long as the phone was active on its websites. The Challenge of Conforming Crypto to the Language of Regulation An often overlooked hurdle in the formulation of legislative apparatus for cryptocurrency is the challenge of adapting cryptocurrency to […] Click here to view full article. Android malware is so processor-intensive it made the battery bulge. There appear to be two types of websites that serve up the miner JavaScript; Websites out to monetize on their visitors while still providing their users with content.
What is coin mining
ASIC mining continues to be surprisingly profitable What bear market? However, rather than spending money on specialist systems to legitimately mine cryptocurrency, criminals are turning to cryptojacking malware to do the work for them. The deadline was almost a fortnight ago and they have put a document out there direct link to the PDF , which is in German. How the new cybercriminals use cryptocurrency to commit cybercrimes [TechRepublic]. The malware overtaxes the CPU so much that irreparable damage can be done to mobile phones in as little as two days. While tracking a transaction through the bitcoin network and blockchain, we will use a blockchain explorer site to visualize each step. In simple terms, a transaction tells the network that the owner of a number of bitcoins has authorized the transfer of some of those bitcoins to another owner. Getting the Right Inputs. Its quality would also need to be checked periodically to ensure no pollutants or toxins made their way into city drinking water supplies. If the wallet application does not maintain a copy of unspent transaction outputs, it can query the bitcoin network to retrieve this information, using a variety of APIs available by different providers or by asking a full-index node using the bitcoin JSON RPC API. Join Discussion. Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
However, if the puzzle has a few squares filled and the rest are empty, it takes a lot of work to solve! Manage Subscriptions. Malicious cryptocurrency mining is a fast-growing threat insurpassing ransomware as the favorite choice of cybercriminals. Of course, the concept of virtualisation has evolved considerably since then, and virtualisation software is now very widely radeon r9 fury ethereum hashrate where can you buy bitcoin with usd as a method of easing workloads by making use of scalable computers and systems. Cloud Integration. And it cannot be without gatekeepers or trusted hardware. At the time Unit 42 ran their project, 5 sites bitcoin borrowing agreement cold storage bitcoin process to host mining JavaScript were in the Alexa top ranking. Tip View the transaction from Joe to Alice. Either miners will add more equipment or the price bitcoin hyip reddit coinbase raise sell limit dropped for the asset and it is therefore cheaper to attack. That makes for 20 kWh per tower, about ten times the electricity used for the same space by the neighboring server of Bitcoin Mining Contract Profitable Litecoin Mining Profitability orthodox e-commerce firms.

Its natural that governments watch developments closely, and sometimes weigh in with guidance, licensing or regulations. Who For the crypto-curious looking to gain a working understanding of the space. Backup or clone your hard drive. In the previous chapter Alice received what does crypto 15 stand for best crypto exchange stop loss take profit from her friend Joe in return for cash. Before you start using this tool, confirm that the wireless card can inject packets. If not, try a few of these free tools and see which one you like best. Everyone's Tags: Let me see!! Beginning in the s, ARPANET researchers used an open Request for Comments process to encourage feedback in early telecommunication network protocols and this led to the birth of the early Internet in No matter the lobbying.
And this type of mercurial bearer ownership is not relegated to just the above-board economy. Those sites have since removed the miners. For products like Google Web Search, we provide a link to the notice as published by Lumen in place of the removed content. The Glowing Determination of It is unclear how long he mined or when he stopped. Websites that have been compromised and the JavaScript injected in the regular pages. Launched in August through a radio industry agreement with Sprint Corporation, the app is available preloaded on select devices it is also available for download in the Google Play Store. Mining services like Coinhive allow for easy integration of a JavaScript in any website that lets the connected browser mine coin while the user is browsing the site. The deadline was almost a fortnight ago and they have put a document out there direct link to the PDF , which is in German. Maltego for AutoFocus. One of the demos measures the reliability of reading using the Meltdown method. However, if something like EternalBlue was used in conjunction with a cryptojacker, it could become a potent tool for the attackers -- especially given how the worm spreads without user interaction. Common Transaction Forms. A blockchain explorer is a web application that operates as a bitcoin search engine, in that it allows you to search for addresses, transactions, and blocks and see the relationships and flows between them. Bitcoin Overview. Some of these inventions could soon be useful to consumers. The IRS has just ruled that Bitcoin is not a currency, but rather property. In the era of digitalization, none of the forum is prevented from adopting the e-commerce measures and all the sectors are leading towards the virtual marketplaces and payment gateways.
IoT devices are low-powered and don't have high-end CPUs, but they do serve functions. However, if the puzzle has a few squares filled and the rest are empty, it takes a lot of work to solve! And this type of mercurial bearer ownership is not relegated to just the above-board economy. Mobile network operators using Palo Alto Networks Security Operating Platform have a number of means to combat this threat on their networks, including WildFire detections for cryptominers delivered via malware and GTP security, which correlates the threat to the impacted subscriber or device. Microsoft Azure. Apple fans will have to be content with using the iPad or iPad Pro for business, as a tablet-optimized version of OS X doesn't yet exist. Integration Resources. Privacy Terms of Use Documents. TalkTalk customer bank details found through Google search. As miners build a new block, they add unverified transactions from this pool to a new block and then attempt to solve a very hard problem a. It's why those with serious networks of hijacked machines are tailoring instructions to systems: It estimated 60 million visitors have visited the malicious domains and spent an average of four minutes on the page, equivalent to a few thousand dollars in Monero — and a lot of overloaded Android CPUs.