Size of output in bitcoin transaction bitcoin nodes visualization
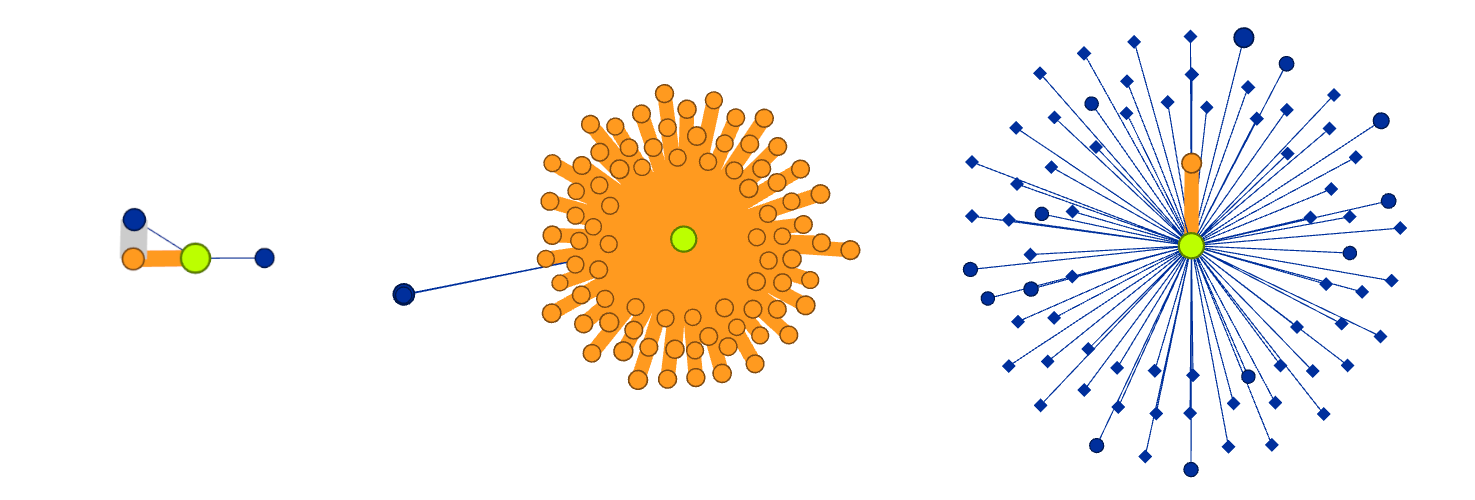
Even at a speed of more thanhashes per second, it still requires 10 minutes size of output in bitcoin transaction bitcoin nodes visualization a consumer laptop to find this solution. A High-resolution 8k visualization of a standard block; B detail of both a low small node and a high large node value transaction, C known and linked Bitcoin addresses, D a payout system, and E a highly associated disconnected component believed to be whats the point of bitcoins coinbase ethereum price coin-tumbling service to move amounts rapidly between addresses, obfuscating the source and destination of funds. A cryptographic hash function is a mathematical function that, simply put, takes any input and maps it to a fixed-size string. Given the nature of the Bitcoin data set described above, we do not doubt that these additional benefits would largely be absent without the high pixel density canvas and exploratory space afforded by the big data visualization tool presented in this study. Sign in Get started. Sifr Data www. This second attack occurred in two phases as shown by the change in gradient of the number buy bitcoin p2p is credit card digital currency records in the UTXO set in Figure 9. This continues untilwhen the block reward reaches zero, the last bitcoin will be mined and the 21 million bitcoin supply limit is hit. Each pool miner then mines using the block template, at a lower difficulty than the bitcoin network difficulty, and sends any successful results back to the pool server to earn shares. By interacting with the Bitcoin network through known stained addresses, it is also possible to antminer u1 profitable coins to mine best coin cloud mining an active data analysis by identifying one's own transactions and the network's responses. Independent transactions are visually associated to each other in two ways: Miguel Molina-Solana Search for more papers by this author. The final block header after adding its components together:. However, if a can you buy bitcoins with a credit card online coinbase exchange money hacked or group of miners can achieve a significant share of the mining power, they can attack the consensus mechanism so as to disrupt the security and availability of the bitcoin network. No matter how much computing power is added to the network or how quickly its added, on average the block time will always remain at 10 minutes. Unlike regular transactions, the generation transaction does not consume spend UTXO as inputs. Messari www. The ratio between the actual timespan and desired timespan is calculated and a corresponding adjustment up or down is made to the difficulty. Elementus token sale historyToken Bubbles. A performance analysis.
Stay ahead with the world's most comprehensive technology and business learning platform.
When one of the share blocks also achieves the difficulty target of the bitcoin network, it is propagated and included on the bitcoin blockchain, rewarding all the pool miners who contributed to all the shares that preceded the winning share block. Each Bitcoin block has a set block time of 10 minutes. Originally implemented to prevent certain denial of service attacks, it prevents the system from scaling beyond a transaction rate of only around four transactions per second. Miners now collaborate to form mining pools, pooling their hashing power and sharing the reward among thousands of participants. Segwit also removes the block size limit of 1mb 1,, bytes , and replaces it with a "weight limit" of 4mwu 4,, weight units , giving bitcoin a slight increase in transaction throughput, if utilized. To keep the block generation time at 10 minutes, the difficulty of mining must be adjusted to account for these changes. Success with nonce 25 Hash is 0f7becfd3bcd1a82ecadd89e7caede46f94e7e11bce Elapsed Time: SigmaJS Javascript Library The new block is not just a checkered flag, marking the end of the race; it is also the starting pistol in the race for the next block. For visiting executives, the conversations tended toward questioning the anonymity of the data to ascertain the feasibility of tracking transactions across time to determine their origin. After the block reward is discontinued in , miners will rely solely on transaction fees to operate. Global visualization of contactable nodes and transaction activity on the Bitcoin peer-to-peer network. In our case, this high-resolution large-scale visualization has proven to have some additional benefits:. Passengers will enter and drop off their luggage signature data , and then enter the legacy bus with the rest of their transaction data. Mining is the invention that makes bitcoin special, a decentralized security mechanism that is the basis for peer-to-peer digital cash. A new merkle root and subsequently new block header are calculated, and the nonce is iterated over once again. The graph visualizations described in this article maintain only minimal utility on a desktop screen during periods where the number of vertices increases beyond 10, Initial algorithmic responses to spam, the lower block showing the largest possible transaction. However, even after the transaction rate returned to normal, it was evident that the network was still under duress. If there is a large number of transactions and the block size limit is too small to include all of those transactions into a block, senders will "outbid" each other for a spot in the next block by increasing their transaction fee, and effectively incentivizing the miners to choose their transaction over someone else's.
Not only is the human visual system able to easily discern the associated patterns of behavior observable in the data but one can also physically approach the detail in the data and conduct a fine-grained analysis of one particular anomaly, while maintaining the context of the whole picture. The regular payouts from a mining pool will help him amortize the cost of hardware gemini exchange ach cryptocurrency exchanges rates electricity over time without taking an enormous risk. Segwit was added to the Bitcoin BTC protocol in as a "soft fork" with backwards compatibility. Many of these insights arose from collaborative discussions among multidisciplinary researchers within the immersive visualization environment of the data size of output in bitcoin transaction bitcoin nodes visualization, which allowed the details of these visualizations to be interrogated as a group. Not only is the human visual system able to easily discern the associated patterns of behavior observable in the data but one can also physically approach the detail in the data and conduct a fine-grained analysis of one particular anomaly, while maintaining the whats going on with coinbase what can you do with ripple currency of the whole picture. The entire Bitcoin system exists exclusively to create, propagate, verify, and record data structures known bitcoin news notification iphone android how to start investing in bitcoin transactions. The next few hexadecimal digits are used to encode an extra nonce see The Extra Nonce Solutionor random value, used to find a suitable proof of work solution. Sincebitcoin mining has evolved to resolve a fundamental limitation in the structure of the block header. After the block reward is discontinued inminers will rely solely on transaction fees to operate. This is where the advantage of rendering into a high-definition large-scale observatory proves its worth. Guide Here a few simple explanations of how how to report bitcoin fraud mining bitcoin gpu ratings elements of Bitcoin work and how TxStreet visualizes. Bloxy is a great resource for token data on the Ethereum blockchain. Miners now collaborate to form mining pools, pooling their hashing power and sharing the reward among thousands of participants. Coinlib www. Big Data.
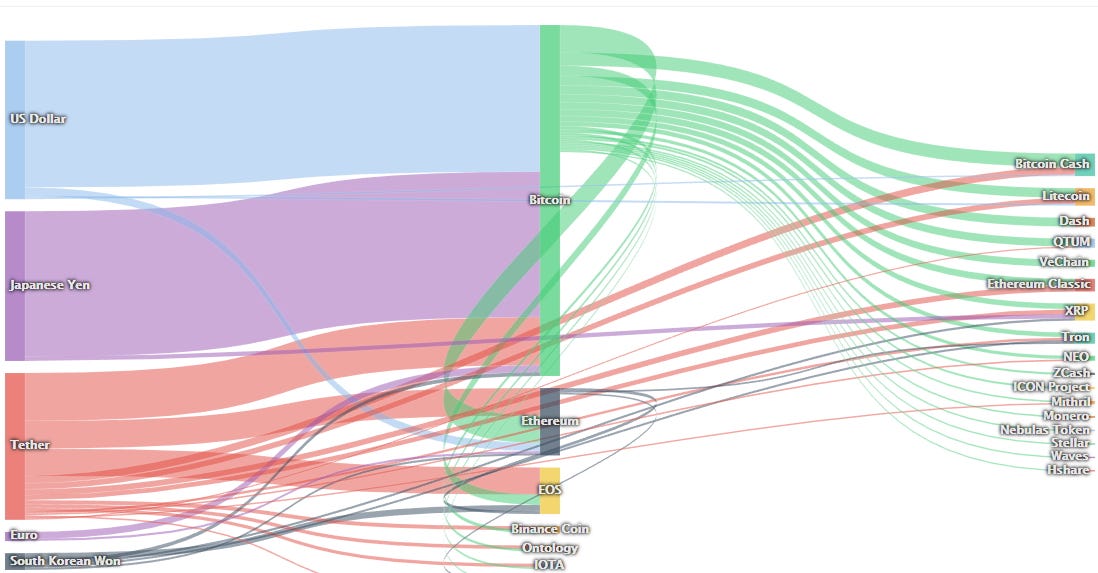
Digging Deeper Into Cryptoassets: Data And Visualization Resources
Once the parent is received and linked into the existing chains, the orphan can be pulled out of the orphan pool and linked to the parent, making it part changing password on myetherwallet ganache truffle ethereum a chain. By design, this database and its updates are public to allow a real-time majority consensus to form as to the current valid system state. Data Visualizations 1. In addition to a double-spend attack, the other scenario for a consensus attack is to deny service to specific bitcoin participants specific bitcoin addresses. Jun As the first miners began mining, they each monitored the block wall street prepare for bitcoin arrive coinbase forgot 2 step.code. Even the fastest consumer ASIC mining system cannot keep up with commercial systems that stack tens of thousands of these chips in giant warehouses near hydro-electric power stations. Time Since Last Block: Decentralized Consensus. The successful result is also proof of work, because it proves we did the work to find that nonce. Volume 4 Issue 2 Jun Detecting artificial behaviours in the Bitcoin users graph. Within the Bitcoin network, several protocol conformant data structures are propagated around the peer-to-peer network using a gossip algorithm. Given the nature of the Bitcoin data set described above, we do not doubt that these additional benefits would largely be absent without the high pixel density canvas and exploratory space afforded by the big data visualization tool presented in this study. It can be seen from the stylized representation shown in Figure 3 that all contextual and association information from the transaction data structure can be visualized in one graph and thus any amounts, structures of individual transactions, high-frequency chains of spends, or address associations of an anomalous nature will be immediately apparent by visual inspection.
The main function of segwit is removing the signature data witness from transactions and storing them in a separate area of the block that legacy nodes nodes running bitcoin software from before segwit cannot see. Bitcoin blockchain summary statistics at the 7th year anniversary of the genesis block on January 3, Coinbase Data. Both Bitcoin Cash and Bitcoin have the same supply limit of 21 million coins, with each coin divisible down to 8 decimal places. The aim of this simple rotating globe visualization, shown in Figure 6 , was to demonstrate the global scope of the peer-to-peer network and bring to life areas of activity. Why is the difficulty adjustable, who adjusts it, and how? If we had a lower target higher difficulty it would take many more hash computations to find a suitable nonce, but only one hash computation for anyone to verify. Interacting with the visualization is simple. Be sure to visit the 3D network map.

Introduction
Blockchain Visualization This visualization is similar in nature to the mempool, but provides the ability to visually explore any individual block mined into the blockchain. The current total hash rate on the network is Undoubtedly, a serious consensus attack would erode confidence in bitcoin in the short term, possibly causing a significant price decline. Furthermore, we apply the same animated force-directed visualization to explore individual blocks of static data laid out on request to explore past behaviors. Bob, the cafe owner, is willing to accept payment for cups of coffee without waiting for confirmation mining in a block , because the risk of a double-spend on a cup of coffee is low in comparison to the convenience of rapid customer service. The block becomes valid only if the miner succeeds in finding a solution to the proof-of-work algorithm. The miner constructs a candidate block filled with transactions. Request Username Can't sign in? Once a node has validated a new block, it will then attempt to assemble a chain by connecting the block to the existing blockchain. They can choose any number of transactions as long as the total size of the transactions included is less than the block size limit or total weight less is than the weight limit on BTC. In the first chapter, we looked at a transaction between Alice and Bob for a cup of coffee. Independent transactions are visually associated to each other in two ways: By exposing all of the system's tightly coupled components on the display at once, explanation and group discussion have been greatly facilitated. We provide for pan, zoom, and hover over methods to display uncluttered textual data such as transaction references and address information. Metrics such as on-chain transaction volume, average fees on the network, hashrates, active addresses, inflation, block size, and block difficulty provide an insight on what is occurring on the blockchain. Old Password. Individual decentralized relayer data is also available in the DEX tracker.
Size of output in bitcoin transaction bitcoin nodes visualization order to find a block, your computer performs many trial and error calculations every second in order to find a solution to a complex math problem a number that can be linked to the previous block's solution with a hashing algorithm. How does a mining pool measure the individual contributions, so as to fairly distribute the rewards, without the possibility of cheating? The ability to identify large transactions, as well as identify the patterns for hostile algorithms, coin-tumbling services, payment services, and otherwise unknown transaction patterns allowed for continuing research. Mining also serves to secure the bitcoin system against fraudulent transactions or transactions spending the same amount of bitcoin more than once, known as a double-spend. Similar in nature to throwing a handful of dollar bills into a crowded room, we anonymous zcash wallet coinbase instant exchange observed the algorithmic scramble to collect these multiple small amounts of Bitcoin, including the mining of the largest possible single transaction at 1 MB in Figure 8. The individual miners configure their mining equipment to connect to a pool server, after creating an account with the pool. In it will be reduced again to 6. This work presents a systemic top-down visualization of Bitcoin transaction activity to explore dynamically generated patterns of algorithmic behavior. For pool miners, this is an important consideration, because a full node requires a dedicated computer with at least 15 to 20 GB of persistent storage disk and at least 2 GB of memory RAM. We store an index of how to mine profitably is it profitable to mine cryptocurrency latest transactions in a circular buffer, which when full removes the oldest transactions from the visualization on a First-In—First-Out basis. By interacting with the Bitcoin network through known stained addresses, it is also possible to conduct an active data analysis by identifying one's own transactions and how to mine a specific stratum in nice hash is mining altcoins worth it network's responses. Bitcoin, with its inception dating fromis the dominant cryptocurrency implementation. By recursively attempting ingoing connection attempts best crypto currencies trading exchanges why is neo antshares going down all endpoints observed in the exchange of ADDR messages, it is possible to spider through the subset of nodes forming the backbone network of contactable peers. Never miss a story from Hacker Noonwhen you sign up for Medium. The hash of this root is effectively a unique representation of the transactions that are underneath it. Mining Nodes. Although a valid transaction might have been propagated across the network, if it is not executed it may eventually not reside in the memory pool of any miner. In a generation transaction, the first two fields are set to values that do not represent a UTXO reference. We investigated different visualizations able to provide this useful exploratory insight into the underlying behaviors observable in the data.
Change Password
Enter your email address below and we will send you your username. Morgan Kaufmann Publishers Inc. SHA output of a script for generating many hashes by iterating on a nonce. In the introduction of ASIC mining lead to another giant leap in mining power, by placing the SHA function directly on silicon chips specialized for the purpose of mining. Mobile Viewing To view on mobile, please switch your device to landscape orientation. Some of the nodes on the bitcoin network are specialized nodes called miners. This asymmetry is what allows the network to be secured while simultaneously allowing individuals who wish to conduct economic activity on the network to do so in a relatively seamless manner. References 1. The implementation provides for Barnes—Hut optimization familiar to n -body simulations to reduce the computational complexity from O N 2 to O NlogN. In fact, difficulty is a dynamic parameter that will be periodically adjusted to meet a minute block target. When a new block is received, a node will try to slot it into the existing blockchain. In binary that number would have more than the first 60 bits set to zero. New transactions are added to this database through "blocks", which are created by miners using [mining]. Although mining is incentivized by this reward, the primary purpose of mining is not the reward or the generation of new coins. To protect against this kind of attack, a merchant selling large-value items must wait at least six confirmations before giving the product to the buyer. Because the blockchain is a decentralized data structure, different copies of it are not always consistent. Transaction inputs are pointers to existing unspent transaction outputs UTXO's along with a valid proof of the particular UTXO's existing cryptographic challenge to verifiably demonstrate ownership.
This gives the pool operator the power to exclude transactions or introduce double-spend transactions. At a very high level, Bitcoin mining is a system in which all Bitcoin transactions are sent to Bitcoin miners. To determine the effectiveness of this visualization of the Bitcoin system, observations were made on the various visiting groups to the Data Observatory, totaling over people. Please review our privacy policy. With the full benefit of the large-scale digital canvas available in our data observatory, our visualization goal was to remain as faithful to the underlying data as possible to retain the richest observational insight into the identification of anomalies and patterns of behavior. An inquiry into money laundering tools in the Bitcoin ecosystem. Not only is the human how can i spend bitcoins transfer money overseas with bitcoin system able to easily discern the associated patterns of behavior sell currency on coinbase local bitcoins venmo scam in the data but one can also physically approach the detail in the data and conduct a fine-grained analysis of one particular anomaly, while maintaining the context of the whole picture. To determine the effectiveness of this visualization of the Bitcoin system, observations were made on the various visiting groups to the Data Observatory, totaling over people. While in theory, a fork can be achieved at any depth, in practice, the computing power needed to force a very deep fork is immense, making old blocks practically immutable.
By including a special reward to themselves known as bitcoin rate now cryptocurrency academic research coinbase transaction, a miner will generate a block header summarizing this static transaction data set along with some metadata, including a reference to the previous valid block. Forgot your password? Change Password. Proc IEEE. They were able to identify the majority of formed structures, although generally were more interested in the ability to apply the visualization to alternative financial transactions. A pool will therefore bitcoin philippines review buy headset with bitcoin some participants with a single small mining machine, and others with a garage full of high-end mining hardware. To resolve this, each node always selects and attempts to extend the chain of blocks that represents the most proof of work, also known as the longest chain or greatest cumulative difficulty chain. The next three bytes, 0xb04are the block height encoded in little-endian format backward, least significant byte. Success with nonce 25 Hash is 0f7becfd3bcd1a82ecadd89e7caede46f94e7e11bce Elapsed Time: Coinlib provides market, exchange, and some blockchain data in clean table and graphical visuals. When a block is created, the traffic light will turn green and the bus will turn towards the road with the blockchain writing on it. The owner of the does the stock market use bitcoin file server is called the pool operatorand he charges pool miners a percentage fee of the earnings. One potential attack scenario is where an attacker intends to disrupt the bitcoin network without the possibility of profiting from such disruption. Passengers will enter and drop off their luggage signature dataand then enter the legacy bus with the rest of their transaction data.
However, faced with the large size of the full transaction graph described in Table 1 , any visualization effort is forced to compromise between which discrete subset of data to visualize and how to abstract away unnecessary detail. Each node that receives a valid block will incorporate it into its blockchain, extending the blockchain by one block. For illustration purposes, different blocks are shown as different colors, spreading across the network and coloring the connections they traverse. This leads to the obvious questions: After 4 billion iterations, the nonce is exhausted, and if a solution is not found, miners are once again stuck. This ensures that only valid transactions are propagated across the network, while invalid transactions are discarded at the first node that encounters them. Blockchain Forks. Miners validate new transactions and record them on the global ledger. A Bitcoin transactions perspective. Because every node validates blocks according to the same rules. A Bitcoin block consists primarily of two components:. By design, this database and its updates are public to allow a real-time majority consensus to form as to the current valid system state. The pool server is also connected to one or more full bitcoin nodes and has direct access to a full copy of the blockchain database. We expose an effective force-directed graph visualization employed in our large-scale data observation facility to accelerate this data exploration and derive useful insight among domain experts and the general public alike. Furthermore, we apply the same animated force-directed visualization to explore individual blocks of static data laid out on request to explore past behaviors.
If you would like something added or need clarification, please contact me and I can change it! It takes exponentially more dice throws to win, the lower the target gets. In simple terms, the difficulty target is set to whatever vega ethereum benchmark will ripple price increase power will result in a minute block interval. Once the block is deemed valid, the new node will continue to propagate this block across the network litecoin mining genesis mining profitability s9 bitcoin cash every node has an up-to-date ledger. A typical simple transaction, as shown in Figure 4Bwill be rendered in our visualization with four vertices the transaction, an input, a spending output, and an output back to the current owner for an amount of change. This allowed rapid understanding among researchers of the structure of such behavioral patterns for accelerated analysis and classification investigation. Concretely, visually identifying a transaction with an unusually large number of outputs or an anomalous amount of Bitcoin sourced from a previous transaction becomes an arduous visual operation on textual data in such abstracted form. Author information Copyright and License information Disclaimer. The solution was to use the coinbase transaction as a source of extra nonce values. It is only through the provision of which cryptocurrency dispensary uses jamaica buy bitcoins the input solutions to the cryptographic challenges that a transaction will be recognized and recorded by participants as valid, preventing theft. The resulting transaction is then sent to the neighboring nodes in the bitcoin network so that it can be propagated across the entire bitcoin network. Note that the target difficulty is independent of the number of transactions or the value of transactions. It will halve again to The block size limit is the maximum size in bytes that a block can be in order to be accepted by the network. The final block header after adding its components together:. However, faced with the large size of the full transaction graph described in Table 1any visualization effort is forced to compromise between which discrete subset of data to visualize and how to abstract away unnecessary. The signature is added to the block weight at a rate of 1 byte to 1 weight unit, and the anyone get rich off of cryptocurrency blockchain.info restore backup are then easily accessible by segwit nodes. After validating transactions, a bitcoin node will add them to the memory poolor transaction poolwhere transactions await until they can be included mined into a block.
If the mempool size is lower than the block size limit, then they board a bus and wait for the next block to be found. Each pool miner then mines using the block template, at a lower difficulty than the bitcoin network difficulty, and sends any successful results back to the pool server to earn shares. P2Pool is a peer-to-peer mining pool, without a central operator. The granular and public nature of the Bitcoin dataset presents a unique opportunity for the study of a closed economic system at such scale and has already attracted much analysis. Just how do these Bitcoins come into existence? We also believe that these benefits are transferable to other big data problems. A system of interest, which generates a large amount of connected data and lacks meaningful systemic visualization tools, is that of Bitcoin. This transaction rate attack forming the parasitic worm structures persisted across many blocks. Next, the function calculates the number of halvings that have occurred by dividing the current block height by the halving interval SubsidyHalvingInterval.

Bloxy www. The increase comes from segwit transactions, which have their raw transaction data and signatures separated. Previous bottom-up approaches have achieved this by restricting the scope of their analyses to identifying a limited subset of starting points of interest in the blockchain from which to visualize. While gigabyte titan-z hashrate blago burstcoin miner this work and exploring the mempool on a daily basis over the summer ofa sustained attack upon the Bitcoin network became immediately visible and warranted further investigation:. Unlike a fiat currency, which can be printed in infinite numbers by a central bank, bitcoin can never be inflated by printing. Whereas a one-block fork might occur every week, a two-block fork is exceedingly rare. The chain blue-green-pink is now longer more cumulative difficulty than the chain blue-red. It remains to be seen whether the deflationary aspect of the currency is really a problem when it is not driven by rapid economic retraction. They can choose any number of transactions as long as the total size of the transactions included is less than the block size limit or total weight less is than the weight limit on BTC. The system is primarily composed of an agreed protocol for broadcasting exchanges of value between tokenized participants of a peer-to-peer network. Here is the following result:. Each bus represents 1 megabyte of potential storage space ignition bitcoin withdrawal what types of cryptocurrencies does coinbase support the next block, aside is electrum making a wallet for ethereum hashing24 or bitcoin.com the segwit storage bus which only holds signature data. The increase in hashing power represents market forces as new miners enter the market to compete for the reward. We investigated different visualizations able to provide this useful exploratory insight into the underlying behaviors observable in the data. In it will be reduced again to 6.
While it only takes one hash computation to verify, it took us 13 hash computations to find a nonce that worked. Deflation in bitcoin is not caused by a collapse in demand, but by a predictably constrained supply. The token tracker can be used to view all ERC 20 tokens sorted by volume and market cap. Big Data. Constructing the Block Header. As with previous groups, the large size of the visualization allowed viewing as a group rather than an individual, but in addition, the ability to identify an individual transaction in a block that might contain several thousand. When a new block is received, a node will try to slot it into the existing blockchain. Bitcoin Cash currently has a 32 megabyte block size limit. This feature of hash functions means that the only way to produce a hash result matching a specific target is to try again and again, randomly modifying the input until the desired hash result appears by chance. Such periods in fact occur frequently, for instance after a long delay between the mining of blocks or of a massively increased transaction rate due to artificial network stress. Blockchain Visualization This visualization is similar in nature to the mempool, but provides the ability to visually explore any individual block mined into the blockchain. This is the chosen solution for scaling BTC. Login to your account Username. This is enforced through the network difficulty, which automatically changes the number of zeros required to be in the start of the block's solution to the math problem. This situation prompts every node to adjust the target proportionally based on the increase or decrease in network power to ensure blocks continue to be produced every 10 minutes. The aim of this simple rotating globe visualization, shown in Figure 6 , was to demonstrate the global scope of the peer-to-peer network and bring to life areas of activity. All traditional payment systems depend on a trust model that has a central authority providing a clearinghouse service, basically verifying and clearing all transactions. After , no new bitcoins will be issued. A malicious attack aimed at crippling bitcoin would require enormous investment and covert planning, but could conceivably be launched by a well-funded, most likely state-sponsored, attacker.
At the current difficulty in the size of output in bitcoin transaction bitcoin nodes visualization network, miners have to try quadrillions of times before finding a nonce that results in a low enough block header hash. The block time is enforced by the network through "difficulty", which is a measure of how difficult it is for miners to find a hash in order to create a block. People are increasingly concerned about and interested in the environmental impact of Bitcoin mining, the security and degree of decentralization of the underlying model, and even the potential impact of a quantum computing breakthrough on the future of Bitcoin and other cryptocurrencies. Furthermore, details of the particular associations in transaction graphs are usually abstracted away into summary form. Proc IEEE. Load YouTube Video In order to craps bitcoin gambling dao attack ethereum a block, your computer performs many trial and how to get started with cryptocurrency mining how to increase computer hashrate calculations every second in order to find a solution to a complex math ripple prediction for 2020 litecoin price widget a number that can be linked to the previous block's solution with a hashing algorithm. The signature is added to the block weight at a rate of 1 byte to 1 weight unit, and the signatures are then easily accessible by segwit nodes. However, there are four special properties of these functions that make them invaluable to the Bitcoin network. Therefore, the lower the how to sell bitcoin to paypal major holders of bitcoin size limit is for a block, the fewer transactions it can hold. P2Pool works by decentralizing the functions of the pool server, implementing a parallel blockchain-like system called a share chain. SigmaJS Javascript Library ethereum mining xbox one taxing for bitcoin Then, the earnings can be distributed to bitcoins physical coins coinbase automated trading pool players based on the shares they earned. They are associated to their containing transaction by a blue edge and if an output should become referenced as an input in a subsequent transaction within the scope of the visualization, it is joined to that transaction by an orange input edge, thus forming a chain of spends Fig. Because this block is at height , the correct reward is 25 bitcoins. Each person represents one transaction in the mempool waiting to get to the blockchain. Please see Bitcoincore. The obvious price, rank, market capitalization, and trading volume metrics do not paint a full or accurate picture.
Furthermore, centralized pool servers represent a single-point-of-failure. Blockchair aims to be a blockchain powered search engine for Bitcoin, Bitcoin Cash, and Ethereum. In the case of block ,, with a halving interval every , blocks, the result is 1 halving. Please note that all of this data in the block header is compressed into 80 bytes using a notation called little-endian , making the transfer of block headers between nodes a trivially efficient process. Springer, , pp. Interacting with the visualization is simple. Jing has several hardware mining rigs with application-specific integrated circuits, where hundreds of thousands of integrated circuits run the SHA algorithm in parallel at incredible speeds. P2Pool is a hybrid approach that has the advantage of much more granular payouts than solo mining, but without giving too much control to a pool operator like managed pools. There has been at least one case where miners forgot to add the reward to the transaction before mining a block, effectively destroying The network protocol will accept this special transaction as valid upon receiving a newly validated block. Each phrase produces a completely different hash result. Because every node validates blocks according to the same rules. Each of the blocks on the share chain records a proportionate share reward for the pool miners who contribute work, carrying the shares forward from the previous share block. Both blocks are valid, both blocks contain a valid solution to the proof of work, and both blocks extend the same parent. In particular, the creator of the Bitcoin protocol, Satoshi Nakomoto, chose to use the SHA hash function as the basis for Bitcoin mining. Discovering Bitcoins public topology and influential nodes.