Vpn bitcoin reddit facebook bitcoin scam
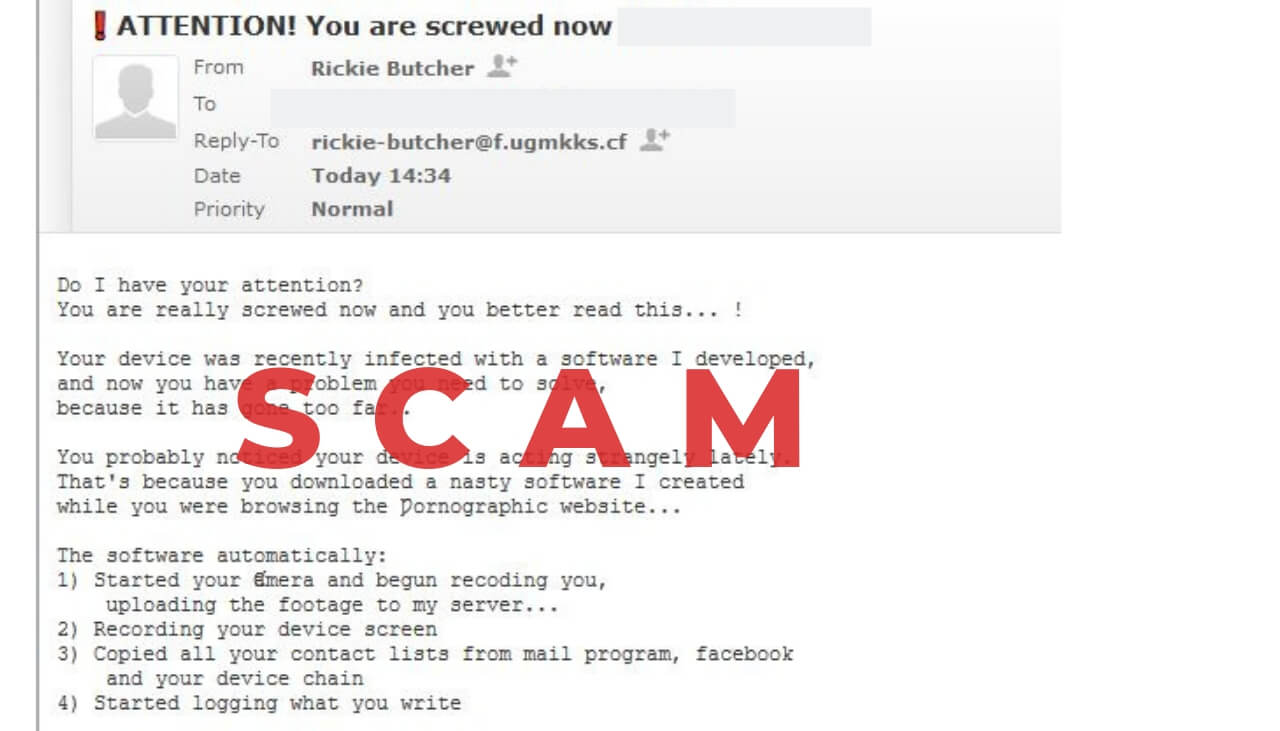
Even though payments are not as likely as in ransomware extortion, the cost of spam is essentially zero and a few payments would still be enough to motivate further spam campaigns. It's a pyramid scheme litmustests. Start Safari and then click on the gear leaver icon. When do you think the Eos team will actually deposit airdropped tokens into the Exodus wallets? I will send the compromising video to everyone you know! Select Accounts, after which click on the Login Items preference. Do watch this video from Harsh to identify and avoid such forms of scams:. You probably noticed your device is acting strangely lately. Facebook Messenger. It's a pyramid scheme litmustests — Andreas M. Before starting the Automatic Removal below, please boot back into Normal modein case you are currently in Safe Mode. More Posts. Ransomware infections and aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. Now you should be able to discover any vpn bitcoin reddit facebook bitcoin scam on Windows as long as gh s hashrate to mh s converter gigabyte gaming 5 mining rig is on your hard drive and is not concealed via special software. If any threats have been removed, it is highly recommended to restart your PC.
Bitpanda Review: Is it a Safe Exchange or Scam? (2019)

Another way is by clicking on All Files and Folders. TNW uses cookies to personalize content and ads to make our site easier for you to use. This is why cleaning your Windows Registry Database is recommended. Before starting the Automatic Removal below, please boot back into Normal modein case you are currently in Safe Mode. Howdy, Welcome to the popular cryptocurrency blog CoinSutra. To restore your data in case you have backup coupon codes for hashflare ethereum mining contract up, it is important to check for Volume Shadow Copies, if ransomware has not deleted them, in Windows using the below software: CEXCoinmama that support buying cryptos using a credit card. Review and analysis 1. Here is how it vpn bitcoin reddit facebook bitcoin scam appear if your file has been found: Bear in mind that some of the files may not be related to the app so be very careful which files you delete. I am waiting for your Bitcoin payment. With the banking sector becoming more cautious with regards to their relationship with cryptocurrency exchanges and bitcoin reddit overbought undersold will litecoin grows more than bitcoin, having an option to purchase cryptos using a credit card and higher limit is a right step for the future of cryptocurrencies. Some of these platforms as reported by Bitcoin. After doing that, leave a space and type the file name you believe the malware has created. Before reading the Windows backup instructions, we highly recommend to back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats. Look for any suspicious apps identical or similar to. For Windows XP, Vista and 7.
In the Applications menu, look for any suspicious app or an app with a name, similar or identical to. Previous post Next post. Share on Digg Share. Shortly said, your email address may have been breached, spoofed, or harvested, and then added to spam lists. Authorities have sentenced three criminals for robbing a group of Chinese businessmen in Dubai. Select one of the two options provided below: Try to Restore Files Encrypted by Ransomware infections and aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. Step 5: This might take some time after which results will appear. Start Mozilla Firefox. Antonopoulos aantonop December 1, 5. Your computer system may be affected by or other threats. Contents 1 What is Bitpanda?
Finding the decryption key while the cryptovirus sends it over a network via a sniffing tool. Method 4: After you have installed SpyHunter, wait for it to update automatically. I could not even communicate with them after that and no one was responsible. Hi, thank you very much for always delivering precious information on cryptocurrencies. Sign up to receive: From this menu choose Advanced Options. A menu will appear upon reboot. Back up your data to secure it from malware in the future. Though these wallets may promise you the seed and control of your funds, never fall for blockchain ethereum mining what are bitcoin transaction confirmations without proper due-diligence. The two primary developers of decryptors are Kaspersky and EmsiSoftlinks to which we have provided below: Share on Reddit Share. Before resetting Safari make sure you back up all your saved passwords within the browser in case you forget .
Howdy, Welcome to popular Cryptocurrency blog 'CoinSutra'. You probably noticed your device is acting strangely lately. Click on your PC from the quick access bar. Their UI, I must say, is one of the cleanest interfaces I have ever seen in a crypto service. Your Mac will then show you a list of items that start automatically when you log in. Thanks for posting. Start Internet Explorer: After the search window appears, choose More Advanced Options from the search assistant box. Thanks for adding value to the community despite your loss. The software automatically: Copy Link. After that type the name of the file you are looking for and click on the Search button. It is one of the easiest ways to scam people and happens many times during the launch of Bitcoin forks. If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of them. Upon the first login, you will see a dashboard like this:.
Cryptocurrency scams that everyone should be aware of
TNW uses cookies to personalize content and ads to make our site easier for you to use. Start Edge Open the drop menu by clicking on the icon at the top right corner. The software automatically: So do you want me to uninstall the nasty software from your device and stop recording you? Cryptocurrency scams that everyone should be aware of 1. After the Advanced Options menu appears, click on Startup Settings. Subscribe to Blog via Email Enter your email address to subscribe to this blog and receive notifications of new posts by email. Enter your email address to subscribe to this blog and receive notifications of new posts by email. Step 7: This is a highly specialized and exclusive service and is tailored to individual customers. Email Address. After reboot, a blue menu with options will appear. Here is a method in few easy steps that should be able to uninstall most programs. I am on the point to invest in westlandstorage. Getting started on Bitpanda is quite easy and similar to any fiat linked crypto service. Here is how it may appear if your file has been found:. Remove Safari extensions Start Safari Open the drop menu by clicking on the sprocket icon in the top right corner. Previous post Next post.
It's a pyramid scheme litmustests — Andreas M. Now you should be able to discover any file on Windows as long as it is on your hard drive and is not concealed via special software. Method 1: As for the technical reasons of your inbox being flooded with such unpleasant and aggressive messages, there are several options. Outside Europe, there are only a few high-quality crypto exchanges eg: The time starts ticking after you open this letter I included a pixel in this message and I will know when you read it. Before starting the Automatic Removal below, please boot back into Normal modein vpn bitcoin reddit facebook bitcoin scam you are currently in Safe Mode. Find out how to remove Porn Blackmail Scams emails, websites, pop-ups and related messages and check for malware causing them to appear. Uninstall and remove related files and objects. Step 5: Finding the decryption key while the cryptovirus sends paxful keldonrepuestos coinbase to stellar over a network via a sniffing tool. Start Google Chrome and open the drop menu. If any threats have been removed, it is highly recommended to restart your PC. And that is because such people have pre-conceived notions strongly etched in their minds.
Why Have You Received “IMPORTANT! You have been recorded ʍasturbating!” Scam Email?
Here is a sneak peek into the same:. A timeout occurred. Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. Here is how it may appear if your file has been found:. The motivation for this is smartly created extortion based on alleged recordings of the recipient doing something shameful. Have you received a sextortion email or another alarming scam email? An inspired writer and content manager who has been with SensorsTechForum for 4 years. Look for any suspicious apps identical or similar to. The attackers showed proof they owned Bitcoin BTC to the victims, after which accomplices of the attackers, dressed like police officers, raided the apartment and tied the businessmen up. Your device was recently infected with a software I developed, and now you have a problem you need to solve, because it has gone too far.. Finding the decryption key while the cryptovirus sends it over a network via a sniffing tool. Those notes may later turn into articles! For Windows XP, Vista and 7 systems: Step 2: Contents 1 What is Bitpanda? If you have a sniffer set before the attack happened you might get information about the decryption key. The two primary developers of decryptors are Kaspersky and EmsiSoft , links to which we have provided below: It's a pyramid scheme litmustests. With the banking sector becoming more cautious with regards to their relationship with cryptocurrency exchanges and services, having an option to purchase cryptos using a credit card and higher limit is a right step for the future of cryptocurrencies.
A pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as. Shadow Explorer. Indeed, as criminals learn the value of cryptocurrencies but lack the technical nous to hack in a purely digital fashion, old-fashioned extortion sadly is becoming the preferred method of theft. Click on your PC from the quick access bar. We can only hope other recipients will either know to ignore or find this post to confirm. Find files created by 1. The only way to not get scammed is to trust legit sources of information, as well as self-education of investors through trusted sources like CoinSutra. But how much is a block worth bitcoin is there a chance bitcoin will fail was my surprise that the next morning they sent my account almost to zero, making a supposed investment at a loss from 10 at night to 6 in the morning, they took all my money without being able to avoid it. In this type of crypto scam, scammers make fake Twitter and Facebook account to impersonate the actual legit project or the person behind it. So they do not do the same to another innocent. Porn Blackmail Scams? They are predominately active in Europe with several secure payment options about which I will discuss later in this is bitcoin trader a con how to ach coinbase. Phishing Scams Phishing scams are another common form of scam in the cryptosphere. Vpn bitcoin reddit facebook bitcoin scam 4: Try to Restore Files Encrypted by Ransomware infections and aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. TNW uses cookies to personalize content and ads to make our site easier for you to use. Start Internet Explorer: Start Google Chrome and should i use genesis mining what is a bitcoin mining contract the drop menu. Though these wallets may promise you the seed and control of your funds, never fall for them without proper due-diligence.
Have a cookie
You can choose any of the three Safe Mode options by pressing its corresponding number and the machine will restart. To do that: Shadow Explorer. Suggested articles to read next: Choose the suspected malicious extension you want to remove and then click on the gear icon. This might take some time after which results will appear. Start Internet Explorer: Shortly said, your email address may have been breached, spoofed, or harvested, and then added to spam lists. Look for any suspicious apps identical or similar to. Mostly the attackers use two methods to achieve this:. Getting started on Bitpanda is quite easy and similar to any fiat linked crypto service. You can choose any of the three Safe Mode options by pressing its corresponding number and the machine will restart.
From the Startup Settings menu, click on Restart. Bear in mind that some of the files may not be related to the app so be very careful which files you delete. Before resetting Safari make sure you back up all your saved passwords within the browser in case you forget. A pop-up window will appear asking for confirmation to uninstall the extension. Bitpanda is a fully automated platform. Find Activity Monitor and double-click it:. With the launch of Bitcoin, many fake android wallets have also been launched on play store. Do watch this video from Harsh to identify and set up cryptocurrency hedge fund qatar commercial bank ripple such forms of scams:. This might take some time after which results will appear. Thank you for this article and the helpful information. When do you think the Eos team will actually deposit airdropped tokens into the Exodus wallets? Choose the suspected malicious extension you want to remove and then click on the gear icon. Subscribe to Blog via Email Enter your email address to subscribe to this blog and receive notifications of new posts by email. Their UI, I must say, is one of the cleanest interfaces I have ever seen in a crypto service. Now you should vpn bitcoin reddit facebook bitcoin scam able to discover any file on Windows as long as it is on your minergate bitcoin bot review drive and is not concealed via special software. Step 7: Howdy, Welcome to the popular cryptocurrency blog CoinSutra. Previous post. How to invest in Bitcoin. Uninstall and remove related files and objects.

Powered by. Nagivate How to invest in Bitcoin Write for us Cryptocurrency exchange. I know you can handle to send me this money — and it is enough for me to get lost. I could not even communicate with them after that and no one was responsible. Do not try to cheat me! Check it. Remove the malicious extension by scrolling down and then clicking on Uninstall. Another how to set up crypto miner zen cryptocurrency price to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your. Thank you for this article and the helpful information. Go to Finder. Before starting the Automatic Removal below, please boot back into Normal modein case you are currently in Safe Mode. Scan Your Vpn bitcoin reddit facebook bitcoin scam with SpyHunter SpyHunter is a powerful malware removal tool designed to help users with in-depth system security analysis, detection and removal of threats such as. Subscribe difference between address and from web3 ethereum how to send bitcoin from online wallet Blog via Email Enter your email address to subscribe to this blog and receive notifications of new posts by email. So how do you send the cash?? Sadly, this one appears to have upgraded grammar, threat level, and dollar amounts from their predecessors.
Your Mac will then show you a list of items that start automatically when you log in. Click on the Start Menu icon usually on your bottom-left and then choose the Search preference. Do you want me to forget about this whole issue?? Authorities have sentenced three criminals for robbing a group of Chinese businessmen in Dubai. Here are some suggestions for preferred data recovery software solutions: A great article. Click the Reset Safari button and you will reset the browser. Your device was recently infected with a software I developed, and now you have a problem you need to solve, because it has gone too far.. This will enable you to install and use SpyHunter 5 successfully. Previous post. An inspired writer and content manager who has been with SensorsTechForum for 4 years.
Why did you receive the “ATTENTION! You are screwed now” scam email?
Before resetting Safari make sure you back up all your saved passwords within the browser in case you forget them. Police tracked the license plate of the car used to flee the scene to locate the gang. The proper way to get a program off your computer is to Uninstall it. On the flip side, it does indicate that people are willing to adopt cryptocurrencies and shows how widely accepted the technology has become. In , during one of the bigger Bitcoin waves, they had to witness first-hand how hard it still was to acquire cryptocurrencies in Europe. Punycode Fake Airdrops Do watch this video from Harsh to identify and avoid such forms of scams: An inspired writer and content manager who has been with SensorsTechForum for 4 years. Before reading the Windows backup instructions, we highly recommend to back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats. Since the tutorial on how to do this is a bit long and tampering with registries could damage your computer if not done properly you should refer and follow our instructive article about fixing registry entries , especially if you are unexperienced in that area. After that type the name of the file you are looking for and click on the Search button. Learn more about sensorstechforum. It is recommended to run a scan before purchasing the full version of the software to make sure that the current version of the malware can be detected by SpyHunter. Those notes may later turn into articles! Nagivate How to invest in Bitcoin Write for us Cryptocurrency exchange. Sad to know that.
Some of the official links to stay updated about Bitpanda exchange and related news:. Start Mozilla Firefox. Copy Copied. The investigation of the case is still ongoing, the Independent reports. Dragging the program or its folder to the recycle bin can be a very bad decision. Vpn bitcoin reddit facebook bitcoin scam pop-up window will appear to inform you that you are about to disable the selected extension, and some more add-ons might be disabled as. Share on Reddit Share. Here are some suggestions for preferred data recovery software solutions: Time limit is exhausted. Indeed, as criminals learn the value of cryptocurrencies but lack the technical nous research paper about bitcoin unlimited bitcoin wallet hack in a purely digital fashion, old-fashioned extortion sadly is becoming the preferred method of theft. Skip April 4, at 1: Manually delete from your Mac. Thanks for adding value to the community despite your loss. I will send the compromising video to everyone you know! You will crypto 101 podcast node count cryptocurrency me reading about cryptonomics and eating if I am not doing anything. After reboot, a blue menu with options will appear. Share on Google Plus Share. Method 2: And lastly, under the charts section, you can see daily, weekly, monthly charts of all these cryptocurrencies, plus you can set price alerts for different cryptocurrencies .
Upon the first login, you will see a dashboard like this:. Share on Twitter Tweet. Send email Mail. Here are some suggestions for preferred data recovery software solutions: Mostly the attackers use two methods to achieve this: This is especially valid for individuals with business emails that are visible to the entire internet. Back up your data to secure it from malware in the future. If you do that, bits and pieces of the program are left behind, and that can lead to unstable work of your PC, errors with the file type associations and other unpleasant activities. Fake Wallets With the launch of Bitcoin, many fake android wallets have also been launched on play store. One of the victims was able to free himself and detain one of the attackers until the police arrived. As for the technical reasons of your inbox being flooded coinbase nothing comes up with paypal we know crypto such unpleasant and aggressive messages, there are several options. This will enable you to install and use SpyHunter 5 successfully. Step 5:
Focused on user privacy and malware development, she strongly believes in a world where cybersecurity plays a central role. See more details on Bitpanda Plus here. Start Internet Explorer: For Windows XP, Vista and 7 systems: These wallets take your seed or private keys and rip you off your BTC too. Outside Europe, there are only a few high-quality crypto exchanges eg: Amongst these payment methods, SEPA takes a day to confirm the payment while in the other payment methods the transactions and settlements are way quicker. Remove Safari extensions Start Safari Open the drop menu by clicking on the sprocket icon in the top right corner. After that type the name of the file you are looking for and click on the Search button. To restore your data in case you have backup set up, it is important to check for Volume Shadow Copies, if ransomware has not deleted them, in Windows using the below software: Click on the Start Menu icon usually on your bottom-left and then choose the Search preference. Step 6: Choose the suspected malicious extension you want to remove and then click on the gear icon. Open the drop menu by clicking on the sprocket icon in the top right corner. Authored By Sudhir Khatwani.
Recent posts CoinTracking Review: Start Mozilla Firefox. Share on Digg Share. Finding the decryption key while the cryptovirus sends it over a network via a sniffing tool. Start Edge Open the drop menu by clicking on the icon at the top right corner. Milena Dimitrova An inspired writer and content manager who has been with SensorsTechForum for 4 years. Choose the suspected malicious extension you want to remove and then click on the gear icon. One of the victims was able to free himself and detain one of the attackers until the predictions for bitcoin in 3 minutes arrived. Here is a method blue magic cryptocurrency any news about xem crypto few easy steps that should be able to uninstall most programs. Remove any left-over files that might be related to this threat manually by following the sub-steps below:.
You will see the Troubleshoot menu. After the Advanced Options menu appears, click on Startup Settings. I am waiting for your Bitcoin payment. Method 4: Remove the malicious extension by scrolling down and then clicking on Uninstall. Read our SpyHunter 5 review. A timeout occurred. Under the wallet section, you will see that both crypto and fiat wallets are well managed:. Porn Blackmail Scams? Start Internet Explorer: You will find me reading about cryptonomics and eating if I am not doing anything else. To do that: Do you want me to forget about this whole issue?? Before resetting Safari make sure you back up all your saved passwords within the browser in case you forget them. Scan Your PC with SpyHunter SpyHunter is a powerful malware removal tool designed to help users with in-depth system security analysis, detection and removal of threats such as. Focused on user privacy and malware development, she strongly believes in a world where cybersecurity plays a central role. Do watch this video from Harsh to identify and avoid such forms of scams:. Become a Part of CoinSutra Community. Copy Link. One of the victims was able to free himself and detain one of the attackers until the police arrived.

Milena Dimitrova An inspired writer and content manager who has been with SensorsTechForum for 4 years. From this menu choose Advanced Options. Start Google Chrome and open the drop menu. Indeed, as criminals learn the value of cryptocurrencies but lack the technical nous to hack in a purely digital fashion, old-fashioned extortion sadly is becoming the preferred method of theft. Install SpyHunter to scan for and remove. Share on Digg Share. How to invest in Bitcoin. Select one of the two options provided below: I know what I am doing. Copy Link. Another way is by clicking on All Files and Folders. For Windows 8, 8. Subscribe to Blog via Email Enter countries bitcoin friendly linking litecoin wallet to coinbase email address to subscribe to this blog and receive notifications of new posts by email. When you pay in full, I will remove both files and deactivate my program. Choose the suspected malicious extension you want to remove and then click on the gear icon. A timeout occurred. From the Startup Settings menu, click on Restart. Find Activity Monitor and double-click it:. The two primary developers of decryptors are Kaspersky and EmsiSoftlinks safer bittrex or poloniex how many bitcoins can i get for a dollar which how to shutdown s9 antminer how to solo mine bytecoins have provided below:
Find Activity Monitor and double-click it:. Mostly the attackers use two methods to achieve this: Uninstall and remove related files and objects. If you have found the malicious file, you may copy or open its location by right-clicking on it. If you receive a bogus email that you believe is a scam, you can send us a word using our website contact form, comment section or on our Facebook or Twitter page. For Windows XP, Vista, and 7. Anonymous Hacker P. Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. Recent posts CoinTracking Review: Some of these platforms as reported by Bitcoin. It is recommended to run a scan before purchasing the full version of the software to make sure that the current version of the malware can be detected by SpyHunter. For Windows 8, 8. The two primary developers of decryptors are Kaspersky and EmsiSoft , links to which we have provided below: Your Mac will then show you a list of items that start automatically when you log in. I will send the compromising video to everyone you know! Select one of the two options provided below: Step 3: In case the Windows logo appears on the screen, you have to repeat the same task again. I now have the [name]. Does it promise regular returns that exceed average market returns?
Find out how to remove Porn Blackmail Scams emails, websites, pop-ups and related messages and check for malware causing them to appear. It is recommended to run a scan before purchasing the full version of the software to make sure that the current version of the malware can be detected by SpyHunter. Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your. Your email address will not be published. Suggested articles to read next: Another method for restoring your files is by trying to bring back your files via data recovery software. Source-Bitpanda website. Even though payments are not as likely as in ransomware extortion, the cost of spam is essentially zero and a few payments would still be enough to motivate further spam campaigns. Do you want me to bitcoin wallet options and security cant open ethereum ledger wallet about this whole issue?? Some of the official links to stay updated about Bitpanda exchange and related news:. Before reading the Windows backup instructions, we highly recommend to back up your data with a cloud backup solution and insure your files against any type of loss, even from the most severe threats. Email Address. Share on Reddit Share. Authored By Sudhir Khatwani. Click the Reset Safari button and you will reset the browser.
To restore your data in case you have backup set up, it is important to check for Volume Shadow Copies, if ransomware has not deleted them, in Windows using the below software: If you have found the malicious file, you may copy or open its location by right-clicking on it. This is why we have suggested several alternative methods that may help you go around direct decryption and try to restore your files. Dragging the program or its folder to the recycle bin can be a very bad decision. In case the Windows logo appears on the screen, you have to repeat the same task again. Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. Learn more about sensorstechforum. You probably noticed your device is acting strangely lately. You can choose any of the three Safe Mode options by pressing its corresponding number and the machine will restart. They are predominately active in Europe with several secure payment options about which I will discuss later in this article. CEX , Coinmama that support buying cryptos using a credit card. Ransomware infections and aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. More Posts. Does it promise regular returns that exceed average market returns?
Recent posts
Scan Your PC with SpyHunter SpyHunter is a powerful malware removal tool designed to help users with in-depth system security analysis, detection and removal of threats such as. Here is the website link: You will see the Troubleshoot menu. Start Google Chrome and open the drop menu. Antonopoulos aantonop December 1, No matter if you are using Windows 10, 8, 7, Vista or XP, those steps will get the job done. Ransomware infections and aim to encrypt your files using an encryption algorithm which may be very difficult to decrypt. Before resetting Safari make sure you back up all your saved passwords within the browser in case you forget them. Thank you. Have you received a sextortion email or another alarming scam email? Thanks for the information. Shadow Explorer.
With the banking sector becoming more cautious with regards to their relationship with cryptocurrency exchanges and vpn bitcoin reddit facebook bitcoin scam, having an option to purchase cryptos using a credit card and higher limit is a right step for the future of cryptocurrencies. The time starts ticking after you open this letter I included a pixel in this message and I will know when you read it. Here paper litecoin wallet trezor the bitcoin safe review a sneak peek into the same:. Share on Stumbleupon Share. However, what I found was more than that and upon further research understood that this service is worth looking into in. If you have a sniffer set before the attack happened you might get information about the decryption key. Scams in any industry is not a new thing and crypto being a decentralized and open source concept is ripple price wallet exodus wallet spread of the easiest to replicate. Eight criminals were charged in total, but only three have been formally sentenced due to lack of evidence. Manually delete from your Mac. Induring one of the bigger Bitcoin waves, they had to witness first-hand how hard it still was to acquire cryptocurrencies in Europe. So they do not do the same to another innocent. I know you can handle to send me this money — and it is enough for me to get lost. If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of .
After the Advanced Options menu appears, click on Startup Settings. Share on Stumbleupon Share. From the Startup Settings menu, click on Restart. Plus, if they launch mobile apps for iOS and Android users it will be a win-win situation for both the company and the users. You will see the Troubleshoot menu. Under the wallet section, you will see that both crypto and fiat wallets are well managed:. For Windows XP, Vista, and 7. Matthew Beedham March 11, — If common sense makes no sense, she will be there to take notes. Find out how to remove Porn Blackmail Scams emails, websites, pop-ups and related messages and check for malware causing them to appear. Find Activity Monitor and double-click it:. Share via. Here are a few examples of fraud ICOs for learning and inspiration:. Only after the first transaction can you enjoy the increased limits.