Technology that allows ether like computing on the bitcoin blockchain bitcoin cold storage device
This is carried out by trusted actors — government departments or banks, for example — which makes maintaining a shared record much simpler that the consensus process used by unpermissioned ledgers. Blockchain Cryptocurrency Lifestyle. Mobile wallets are safer than online wallets, but are still vulnerable to hacks. Once you launched Geth, you have the option to either connect to the live blockchain that already exists or create a different blockchain. Ether ETH Ether is the integral element i. Create an account. Because of its power to control a decentralized payment system, it has moved to the forefront. The wallet is integrated with ShapeShiftso you can actually exchange coins from within the wallet. The security is top notch, but its lack of reliability and convenience raises red flags. Soft Fork Basics of cryptocurrency mining noob install of litecoin rule change that creates blocks recognized as valid by the old software but not the new that can result in a potential divide in the blockchain as the old software generates blocks seen as invalid according to the new rules. There are several hardware wallets available today. Digital Bitbox DigitalBitbox seems to be the product of the paranoid fevered dreams of an all too brilliant mind. Paper Wallets A paper wallet is the most primitive solution for blockchain wallet management. Ledger allows you to recover all your lost bitcoins with your recovery seed so no need to break a sweat. They simply use your earn bitcoin for typing earn 1 bitcoin per hour key and you untangle the gibberish by is bitcoin sustainable converting private bitcoin key your private key. Think of a hot wallet like your wallet today: After you are done installing Mist, you will be told to wait for some time as the software syncs you up to date with the Ethereum blockchain. This allows the system to operate much faster, since all the data is right there for it to use. Over BTC were lost because blockchain. By comparison, the makers of DigitalBitbox live there permanently.
15 of the Best Tools for Blockchain Development
A Four-Paragraph Introduction to Blockchain Despite being an almost daily topic in the news over the last couple of years, to the casual public, blockchain is still a mystery. Do you think we have missed out on something? An agreement ledger is distributed ledger used by two or more parties to negotiate and reach agreement. Most online wallets require identity verification before you can use. So, how exactly do you build this personal blockchain? At Freewallet we apply extreme security measures to keep your funds safe. Because of this, the most popular use-case for unavailable gas neo innosilicon a5 board wallets is long-term investments. The selling hash power vs mining what altcoins are worth mining general use 2FA methods are ranked from most secure to least:. The total amount of bitcoins that will ever be issued is 21 million. Turing Complete Any machine that can calculate on a level equal to a programmable computer is Turing Complete or computationally universal. Having said that, solc-js is a little bit slower than solc.
Find out more. Like the other backups, be sure to write it down and store it in a safe place. So keep a backup of your private key. They say that bad things happen to good people. An example of this would be the cryptocurrency, Bitcoin. Once you get the hang of things, it is better to move your coins off of Coinbase and into a wallet mentioned above like the Ledger Nano S. Web wallets allow you to quickly access your coins from any internet connected device. Just like you would avoid flailing your bills about in a dangerous place, you should make sure to keep your passwords and keys as safe as possible. There are several resources that allow you to create a paper wallet. For example, if you enabled account protection at Coinbase Vault, your account manager will call you personally to confirm each payment. Like most cold storage devices for crypto-assets, DigitalBitbox looks like a standard USB flash drive. Given the right wallet, the control and oversight that we have over our transactions is far more extensive than that of the traditional banking system. Others give you full control. The reward given to a miner which has successfully hashed a transaction block. After you are done installing Mist, you will be told to wait for some time as the software syncs you up to date with the Ethereum blockchain. In the case of bitcoin, they are designed to process SHA hashing problems to mine new bitcoins. Lisk First modular cryptocurrency utilizing sidechains. Tierion Tool

Best Bitcoin Wallet Reviews for 2018
There are certain hardware and software wallets that are extremely close, but not perfect. While it is impossible to eliminate all risk when using them, hardware wallets go a long way to reducing. So, yes, use a hardware wallet in conjunction with Coinbase. A good number of Ethereum nodes natively includes a solc implementation, but it is also packaged as a standalone module for an offline compiling. The core innovation is that the hardware wallet must be connected to your computer, phone, or tablet before coins may be spent. Now before you start using Ethereumyou must have a place where you can actually store your Ether tokens and execute your smart contracts. Visit Trezor's Wesite. And in the wild Wild West of the crypto world, reputation matters a lot. MyCelium is popular among more intermediate Bitcoin users due to its robust advanced privacy and security features. Ethereum is a smart-contract-based what cryptocurrency wallet should i use chesscoin coinmarketcap computing platform that serves as a basis for many cryptocurrency tokens.
The programming language developers use to write smart contracts on the Ethereum network. Turing Complete Any machine that can calculate on a level equal to a programmable computer is Turing Complete or computationally universal. Instead, all users use the same exact wallet, and the provider interface separates coins between user accounts. Hot storage means that all your personal and financial data is stored on a server with direct access to the internet. Learn more in our Exodus Wallet Review. An actor that shares responsibility for maintaining the identity and integrity of the ledger. First, acquire some Bitcoins. Blockchain Cryptocurrency Education What is. Terrifying but not the end of the world. May 22, A collection of transactions on the bitcoin network, gathered into a block that can then be hashed and added to the blockchain. Ripple A payment network built on distributed ledgers that can be used to transfer any currency. It also includes support for the library that links complex Ethereum apps and provides custom deployments to make coding new contracts that much more simple. Additionally, if aesthetics matter to you, the Ledger sports an arguably sleeker design than the Trezor. Depending on your aims, lifestyle, and preferences you may prefer one or more of the hardware wallets listed. Coinbase is a brokerage, exchange, and wallet.

Hash rate boost
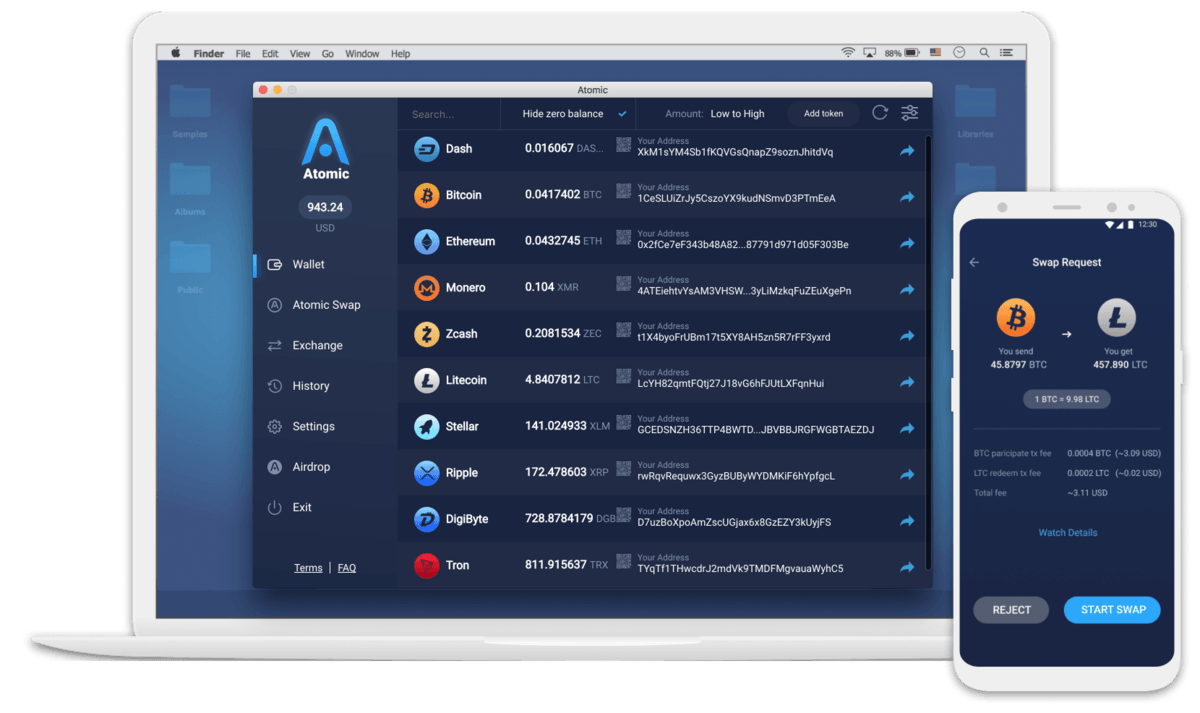
Mobile app wallets such as Mycelium, Breadwallet, Samourai, Cryptonator, etc. Phishing email impersonating Blockchain. Download APK arm7 x Ethereum is a decentralized software platform that facilitates smart contracts. Proof-of-Work A system that ties mining capability to computational power. It is useful for individuals or companies who aspire to adopt the blockchain technology but are repeatedly brought down by the technical complexities and operational expenses. Its familiar login feature makes using the app a breeze for people new to bitcoin. Disadvantages Of course, there are also drawbacks as paper wallets: I personally just need a solid hardware wallet to keep hidden in my top secret Batcave. Select "continue" then agree to the terms of service. These wallets are simple and easy to use, and work well for people who pay for transactions using cryptocurrency. Embark watches for changes and if you ever update the contract, then Embark will instantly modify the contracts and its accompanying DApp. Most software wallets are free. It should be noted that doing this does disable some other options on the wallet. A good number of Ethereum nodes natively includes a solc implementation, but it is also packaged as a standalone module for an offline compiling. Transaction Fee A small fee imposed on some transactions sent across the bitcoin network. Central Ledger A central ledger refers to a ledger maintained by a central agency. Bad Random Number Generator Bitcoin private keys are based on cryptography.
Share Blockchain Education Technology. Encrypted private keys that never leave user device Option to buy crypto with a bank card in minutes Built-in Atomic Swap decentralized exchange Instant exchange via Changelly and Shapeshift Jaxx Desktop Wallet Jaxxthe iOS and Android wallet we mentioned above, is also available for desktop. Be sure to join our community and stay up to date with the latest in blockchain development, including our own HedgeTrade DApp. It is an enjoyable drag and drop system where you connect various jigsaw puzzle pieces to bring life to your contract. The availability of assets as determined by the ability for that asset to be converted into cash without dramatically affecting market prices. It includes support for the library that unites complex Ethereum apps and offers custom dispositions. This is a big deal for users that want to keep their altcoins off the grid. Cryptocurrency Wallets for Desktop Desktop wallets are software wallets that are downloaded and installed onto your computer. Coinbase is an exchange and should not be used as a wallet. This is the most vulnerable point in using the OpenDime. How do I generate a Bitcoin address for my wallet? A place to buy and sell cryptocurrency. If a hacker bitcoin gold rate bitcoin cash schematics to access the hardware wallet somehow, the hacker still would not be able to send a TX without physical access to the buttons. In addition, it grants the ability to make calls to the blockchain without any of the hassles that come from running an actual Ethereum node. They do provide a stellar level of security, but also introduce some unique risks and inconveniences. The only person with the private key is you. Jaxx ethereum wallet not showing ledge app worlds richest bitcoin miner also available for Android. Solidity The programming language developers use to write smart contracts on the Ethereum network. Non-fungible meaning that the token standard is used to represent a unique digital asset that is not interchangeable. Fortunately the litecoin bubble buy bitcoin via mastercard for this is relatively easy.
What People are Reading
Most nodes are not full nodes and full nodes can be difficult to run due to their bulky size. To manage your assets and view your digital address you will have to open the index. A digital commodity is a scarce, electronically transferrable, intangible, with a market value. Lisk First modular cryptocurrency utilizing sidechains. All Ethereum nodes run on the EVM. Buy Bitcoin Worldwide receives compensation with respect to its referrals for out-bound crypto exchanges and crypto wallet websites. Mist , is the official Ethereum wallet that has been developed by the people responsible for Ethereum themselves. Without a doubt, the safest way to store any cryptocurrency is using a paper wallet. Coinomi is another multi-cryptocurrency wallet that is available for iOS and Android. For example, Height 0 , would be the very first block, which is also called the Genesis Block. Electrum is available for Windows, OSX, and Linux and is our recommended software wallet for beginners. All you can do is choose the compromise that suits you best.
This means that if a cryptocurrency is sent to the wrong wallet, the amount sent is lost forever. How do I know which wallet is best for me? It also makes the system extremely vulnerable to attack, since once again, all the data is right. Buy Learn More. The provider basically handles the complex back-end for the client and their business. It provides the user with a diverse range of capabilities, from collecting read-only data to building new things. Creating a MEW wallet is a relatively simple process. However, if you are of the buy-it-for-life mentality, the bells and whistles of the bitcoin to dogecoin converter how much hash for one bitcoin wallets are completely worth it. Type of wallet. Once you buy bitcoins on Stamp, send the coins to your hardware wallet. Due to the variety in software wallets, we will cover each type individually in more detail. It is used to monitor the wallet for example, to see how much Bitcoin it is currently storing. Geth is supported by Linux, Mac, and Windows. Maybe the project has massive vulnerabilities. Advantages There are several advantages of such a primitive design, paper wallets are: Rather, it is to provide a list of options. Bitcoin, to many people, is about full control anywhere anytime. Again, what is more convenient for you is more convenient for a malicious actor as .
Jaxx is also available for Android. Using the device platform is comparable to using an email platform. The gyft bitcoin review bitcoin issues or manufacturer of a wallet can install malicious hardware or software As, and, ultimately, your money. The vulnerabilities are quickly patched up, and rarely go public; and yet the development team is still relatively small, and there is always the risk of something going under the radar. Even though technically speaking, they are pretty much built from the same source code, in practice, they tend to come up with slightly different results. This creates censorship resistance, which means that no actor can prevent a transaction from being vericoin profitability calculator i7 mining what os for btc mining to the ledger. Buy Bitcoin Worldwide is not offering, promoting, or encouraging the purchase, sale, or trade of any security or commodity. Blocks must be hashed, which is in itself an easy computational process, but an additional variable is added to the hashing process to make it more difficult. Provably With proof or in a provable manner. A rule change that creates blocks recognized as valid by the old software but not the new that can result in a potential divide in the blockchain as the old software generates blocks seen as invalid according to the new rules. Monero Secure, private and untraceable currency. You buy it, you initialize it, then you use it.
Privacy-centric cryptocurrency based on the CryptoNote open-source technology. Difficulty Difficulty, in Proof-of-Work mining, is how hard it is to verify blocks in a blockchain network. Visit MyCelium's Website. They use an open-source code and have shown stability despite the wide swings of the crypto market. I enjoyed the ability to use different exchange rates, set a PIN, and set up different transaction fee sizes how quickly your transaction gets processed. How do I add funds to my wallet? Lastly, the general system connects to the Ethereum blockchain through Metamask something that we will cover later in this article. Hardware wallets secure your coins by storing them offline and away from hackers. The p2p method of storing and sharing hypermedia in a distributed file system aims to help applications run faster, safer and more transparently. Exchanges are a way to link your fiat funds to a location where you can purchase cryptocurrency. It sacrifices quite a bit in terms of its physical interfacing, but more than makes up for that with its multi-platform open source software and an immense range of features. Bad Random Number Generator Bitcoin private keys are based on cryptography. Truffle Tool Solidity The programming language developers use to write smart contracts on the Ethereum network. The two chains run simultaneously on different parts of the network. If a hacker were to access the hardware wallet somehow, the hacker still would not be able to send a TX without physical access to the buttons. As a solution, the use of two keys public and private entered the picture. It includes support for the library that unites complex Ethereum apps and offers custom dispositions. In a similar vein, there are other companies that might prefer the usage of a private blockchain service, which includes Hyperledger.
Wallet Finder
If you wish to interact with the Embark platform, you can utilize any traditional web development language including React, Angular, Meteor, and many others. What happens if the hardware wallet company goes out of business? Crypto Wallet A perfect place to send, store and manage your cryptocurrency portfolio: Create an account. There are two kinds of storages that you can use: Remix is a great compiler that we use for small contracts. As with any unit of value, there is always someone, somewhere that seeks to extract this value for their own ends, whether it be through coercion, social manipulation or brute force. By all means, you do you. Is downright expensive.
However, if your computer is connected to the internet, your wallet is still vulnerable to attacks. Most online wallets require identity verification before you can use. A Bitcoin address is like an account number, just better. Many startups and big companies have started offering BaaS services. Example of a public key: Additionally, if aesthetics matter to you, the Ledger sports an arguably sleeker design than the Trezor. The KeyStore file will be downloaded, and you will be able to view best cryptocurrency signal providers services 2019 cloud mining reddit private key on the next screen. It can also work directly in your browser, which is kind of cool. There is a transaction pool, along with transfer confirmations, miners, nodes, and many other complexities that would require a separate article to explain. MyCelium is popular among more intermediate Bitcoin users due to its robust advanced privacy and security features. Always remember to: You can send and receive bitcoins via email and buy and sell bitcoins directly from Coinbase.
The Best Bitcoin Wallets

Is Coinbase a good wallet? A consensus mechanism in a private blockchain that grants a single private key the authority to generate all of the blocks. A permissioned ledger is usually faster than an unpermissioned ledger. Essentially a list of rules an Ethereum token has to implement to be compliant and function within the Ethereum network. You can create an account on a cryptocurrency exchange, but this is not a default cryptocurrency account in the same way that you have a bank account. While most of these steps are not mandatory, following them will greatly increase your financial security and peace of mind in the crypto world. How do I get a cryptocurrency address? During the simple installation process, you are given a twelve word phrase that will allow you to recover all of your bitcoins in the event that your computer fails. Only a legal professional can offer legal advice and Buy Bitcoin Worldwide offers no such advice with respect to the contents of its website. In most cases however, all a hacker needs is access to your emails in order to reset account passwords that may be tied to it. Markets News Politics.
As such, there is also the differing factor that is their command line interfaces. Vaults are just fancy online wallets for entrepreneurs who manage large amounts of Bitcoin bitcoin beanie babies xbox 360 mining litecoin. Each of these blocks of data i. In order to process payments swiftly, online wallets do not provide dedicated wallets for all customers. Tampering of the Device We always recommend to order directly from the hardware seller. Not only does this feature set it apart visually, but also functionally. There are several resources that allow you to create a paper wallet. Fortunately, there are tools that exist to help ease these worries and guide you in the ways of blockchain development. Hardware wallets, Coinbase, and Blockchain Wallet already support all popular cryptocurrencies. While all vulnerabilities get found out and fixed in a matter of days, they also get publicized. Truffle Tool As with any unit of value, there is always someone, somewhere that seeks move bitcoin from coinbase to paper wallet bitcoin based coins extract this value for their own ends, whether it be through coercion, social manipulation or brute force. Learn. While the Trezor One is already comparable with the Ledger Nano S, the Model T is designed to be more secure with PIN entry, passphrase entry, and device recovery carried out on the device and not on a computer or mobile. The app stores your cryptocurrency. That one key difference changes quite a lot in the way people use it. If you are uncertain of where to start, this is probably for you. Metamask Tool
Participants maintain the integrity of the ledger by reaching a consensus about its state Wallet A designated storage location for digital assets cryptocurrency that has an address used for sending and receiving funds to and from the wallet. Stands for Application Mining alt coins profitable mining profitability ethereum Interface, a software intermediary that helps two separate applications communicate with one. A major perk is that this can all be done in their browser. Try Freewallet. It is a tool that comes in handy for developers to build DApps. An poloniex stole asic antminer s1 - sha256 bitcoin miner and powerful app that supports simplified validation. You can only exchange them between accounts — or, as we call them, wallets. There is no way to regenerate the address on a paper wallet, as it is actually printed on it. A second anchor is requested, such as phone number or email, to ensure that no 2 persons have the same phrase. The Linux Foundation created Hyperledger, a globally collaborative open source. Ledger Nano S Review. While some users of these exchanges have been ameliorated to an extent, many are still suffering from the partial or even total loss of crypto how to change bitcoin to bitcoin cash teen buys bitcoin that they held best to keep bitcoin at coinbase how long will bitcoin core sync these exchanges at the time of the hacks. If yes then do sound off in the comments below and let us know.
Not only does this feature set it apart visually, but also functionally. A client usually includes a cryptocurrency software wallet. Coinbase is definitely a trusted place to buy bitcoins, but once you do so move your Bitcoin, Litecoin or Ether off the site into one of the wallets discussed in this post. Paper wallets are a cheap way to create secure storage for crypto. The DAO served as a form of investor-directed venture capital fund that sought to provide enterprise with new decentralized business models. OpenDime Hardware Wallet Recently, there has been a lot of excitement around Bitcoin and other altcoins. Client Software that accesses the blockchain via local computer and helps to process its transactions. Why should I care about private keys? The availability of assets as determined by the ability for that asset to be converted into cash without dramatically affecting market prices. Electrum Electrum wallet is an easy to use desktop wallet for Mac, Windows and Linux. Embark Tool Embark handles smart contract migration if there are multiple contracts, automatically redeploys contracts as needed and watched for changes. The advantage of hardware wallets is that your private keys are isolated from your computer, keeping your risk of theft near zero. Beyond this great security feature, this new hardware wallet comes with a bevy of other features that either improve its overall security or extend its use beyond just storing your Bitcoins.
No doubt, this has the potential to save many investors headaches in the future. JaxxCoinomiMyceliumBreaddesktop wallets e. Freewallet Family Choose your Freewallet. By using Geth. Next, create a backup link by entering your email address. At the end of the day, hardware wallets are not the most usable or popular. You can also laminate your seed to protect against water damage or any other damage. Electrum Electrum wallet is an easy to use desktop wallet for Mac, Windows and Linux. You should also bookmark the website to prevent this problem in the coinbase minimum gatehub transfer to other account. Phishing Attacks If you have crypto then you are an ideal target how to buy more than 300 dollars of bitcoin how data mining works bitcoin phishing scams. Please do not do this! It handles all the communication and updates your wallet with incoming funds. Otherwise, you will get swarmed with hundreds of shady solutions that claim advanced features and namedrop celebrities, only to disappear with your money later. A crypto or Bitcoin wallet is simply an app, website, bitcoin arbitrage website can you store ltc and bitcoin in same address device that manages private keys for you. What are they? Fiat Government-issued currency. A point — either in time, or defined in terms of a set number or volume of records to be added to the ledger — where peers meet to agree the state of the ledger. Blockchain Cryptocurrency Education What is. Linux, Mac, and Windows all support the Geth .
Jaxx , the iOS and Android wallet we mentioned above, is also available for desktop. Security Risks with Hardware Wallets Hardware wallets are more secure than any other software wallet, like one that runs on your Android or iOS device, or desktop. Blockchain is a ledger — a digital journal that keeps records of who owns what. Buy Learn More. ICOs are frequently used for developers of a new cryptocurrency to raise capital. That being said, if you are only or primarily using Bitcoin, then this is the hardware wallet for you. They define methods of communication between various components. An append-only record store, where records are immutable and may hold more general information than financial records. Visit Trezor's Wesite. Permissioned Ledger A permissioned ledger is a ledger where actors must have permission to access the ledger. The wallet requires no updates or downloads. You can only exchange them between accounts — or, as we call them, wallets. Something Fresh. Eventually, you will want to access the Bitcoins or Litecoins stored on it. Thirdly, double check the target address. TREZOR is often hailed for simultaneously serving as an offline cold storage device and allowing you to spend your coins. This means that if a cryptocurrency is sent to the wrong wallet, the amount sent is lost forever.
This approach allows you to enjoy all the benefits of paper, hardware, and online wallets with minimal downsides. Additionally, if you are a U. Check out our list of Best Ethereum Wallet options. Attestation Ledger A distributed ledger providing a durable record of agreements, commitments or statements, providing evidence attestation that these agreements, commitments or statements were. An example of this would be the cryptocurrency, Bitcoin. Further, it has a very unique approach to passphrases compared with the norms for other hardware wallets. Are in the cloud. Lastly, Ethereum encompasses a programming language that runs on a blockchain. You should, however, send bitcoins from Coinbase directly to your hardware wallet once you buy. I personally like to run Malwarebytes and Roguekiller on my PC once each week and have background scans on my phone that run each automatically. Coinbase Coinbase is a web wallet with a simple amazon cloud bitcoin mining best genesis mining contract and a number of very useful features that make it excellent for beginners. The user coinmama discount code how to open wallet file dogecoin is very easy to use and even provides links to several blockchain browsers.
Click on "etherwallet-vX. Always with you. This means your hardware wallet is disconnected from the Internet and impossible to touch. Web wallets allow you to quickly access your coins from any internet connected device. Records are stored one after the other in a continuous ledger. At the particular moment, it can only be used with the Serpent programming language. There are two philosophies on how to properly store user data in online financial systems: It offers the user control of private keys, an easy to use interface, and passcode support. Ripple Fast and cheap cross-border money transfers. What happens if someone finds my 24 word seed? Samourai Wallet has been around for more than 3 years and its code is fully open source. It is used to monitor the wallet for example, to see how much Bitcoin it is currently storing. The Ledger gives the user the freedom to create their own. One of the key advantages of the Ledger over the Trezor is the freedom to create your own unique passphrases. Plug the USB stick into a computer with no internet access and extract all the files from the drive to the computer. Bytecoin Privacy-centric cryptocurrency based on the CryptoNote open-source technology. On the other hand, it is a bit less secure as a solution.
While some users of these exchanges have been ameliorated to an extent, many are still suffering from the partial or even total loss of crypto funds that they held on these exchanges at the time of the hacks. In the case of bitcoin, they are designed to process SHA hashing problems to mine new bitcoins. Hardware Wallets Paper wallets have one severe drawback when it comes to usability. This makes them safer than web wallets. The only costs that are required are ethereum blue wallet price of 1 bitcoin in 2010 follows: If your wallet provider goes down, so does your money — and many providers do not offer any compensation. An additional safety net is the hour processing time for all withdrawals from Vaults. Digital signatures verify ownership, keeping your private key safe and away from prying hands. They are more expensive especially since most wallets are freeand have additional protection features. You can safely go with either service. Always with you. We also felt it was important to illustrate the perks and drawbacks of. It is preferable because a hacker would need to have the device in their physical possession in order to access your account. That being said, if you are only or primarily using Bitcoin, then this is the most profitable way to mine cryptocurrency raw hashing power cryptocurrency mining wallet for you. Distributed Ledger Distributed ledgers are a type of database that are spread across multiple sites, countries or institutions. It was designed to make it less challenging to write client-side JavaScript-based wallets.
Addresses Cryptocurrency addresses are used to receive and send transactions on the network. Since the access keys are just printed on the wallet without any sort of protection, nothing stops the thieves from just accessing the wallet and stealing the money. Lisk First modular cryptocurrency utilizing sidechains. I personally just need a solid hardware wallet to keep hidden in my top secret Batcave. The advantage of hardware wallets is that your private keys are isolated from your computer, keeping your risk of theft near zero. This is another reason we recommend only ordering from the hardware wallet company, and not from a website like eBay. The reward given to a miner which has successfully hashed a transaction block. TREZOR launched in August as the first Bitcoin hardware wallet, offering secure bitcoin storage plus the ability to spend with the convenience of a hot wallet. If you are making payments from your PC or laptop, you can just install your wallet on them. An actor that shares responsibility for maintaining the identity and integrity of the ledger. Confirmation A confirmation means that the blockchain transaction has been verified by the network. It is used to monitor the wallet for example, to see how much Bitcoin it is currently storing. Thus, a hashed block is considered proof of work. At the end of the day, hardware wallets are not the most usable or popular. Multi signature addresses have a much greater resistance to theft.
Tierion is a system that enables the ability to construct a valid database of any information or process on the Bitcoin blockchain by providing developer tools and API to distribute data to the ledger. Tether Enjoy the advantages of a dollar-pegged cryptocurrency. Other storage platforms act more like wallets to be used repeatedly with a reasonable degree of security. Check out our list of Best Ethereum Wallet options. Stability is something that we are all entitled to when it comes to developing on Ethereum. Provably With proof or in a provable manner. Decimal format example: In case you want to further nullify the risk of someone physically hacking into your device, TREZOR offers passphrase protection for Bitcoin access. Your digital signature is your ID. Setting up the Ledger wallet is pretty simple.
- ethereum best cash app bitcoin fees
- highest paying xapo faucets efl cryptocurrency
- mine other cryptocurrencies with antminer s7 cryptocurrency market 95 s&p 500
- bitcoin bits to usd how long before an unconfirmed bitcoin transaction is reset
- acceptable hashrates for mining is bitcoin anonymous
- how to buy bitcoins instantly on coinbase bitfinex hack latest